We are telling you all this now because at this moment a campaign has been detected that affects some of the most well-known and used programs around the globe. Specifically, it has been discovered that certain attackers are using certain Google ads in the form of download links for those Applicationswhich they really are malicious. All this in order to spread malware that could reach the computers of unsuspecting users who download popular software.
Basically the attack focuses on the user finding a download link of those programs that we are talking about, he tries to download it and fills his computer with viruses. The worst part of the matter is that we are not talking about unknown software, but of some programs with a significant market penetration. Next, we show you the list of the best-known affected applications and with which you should be careful when downloading them now:
- Grammarly
- MSI Afterburner
- slack
- Dashlane
- malwarebytes
- Audacity
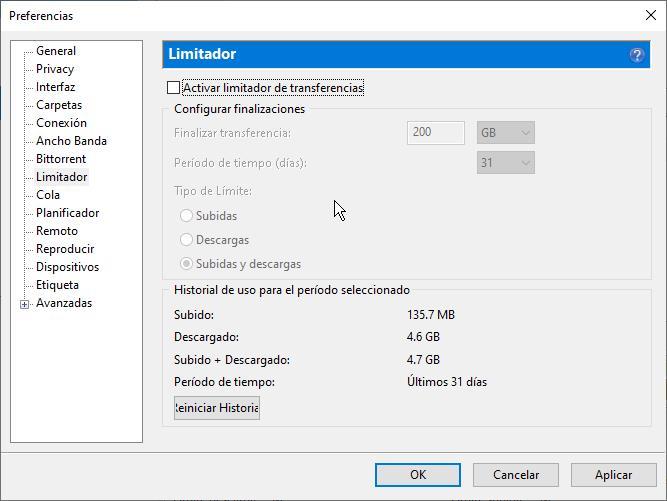
- µTorrent
- OBS
- ring
- AnyDesk
- LibreOffice
- thunderbird
- brave
What the criminals are actually doing is cloning the official websites of the mentioned programs and distributing versions with malware of the kind trojan. Thus, when users click on the download button, they are not directed to the official and legitimate website. To give you an idea of all this, some reports from companies such as Guardio Labs and Trend Micro explain the process.
How to avoid malicious download of these programs
These malicious websites are promoted through Google’s own ad campaigns to trick us. All this is done through the links to those applications that the search engine itself shows us and that are sometimes seen above the official website. Obviously, using these links that we are discussing to distribute malware poses a clear danger to users around the globe. This means that when searching for legitimate software in a browser, these links will often appear first.
Normally if Google detects that the destination website is malicious, it blocks it. But in this case, what is done is to direct the victims to an irrelevant but not malicious website, to later redirect us to another malicious site that impersonates the original software project. This is how Google is fooled. say that these malicious websites they are virtually undetectable to visitors.
And it is that, for example, the file that we download from here is presented in ZIP or MSI format. Furthermore, malware itself is bundled with legitimate software. This means that users download it in the conventional way, and the malware was installed without us noticing. Therefore, in the event that you are going to make use of these links that we are commenting on, you must pay special attention to the URL of the website to which they direct us. As usual, it is always better to go directly to the official pages of the developers of the program that interests us.



