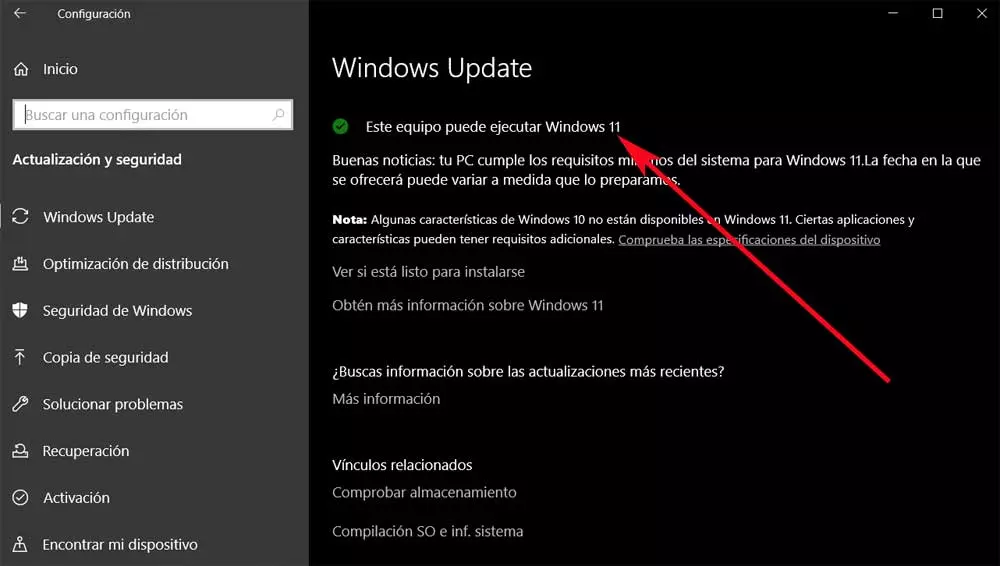
Despite the success of Windows 10, for a few months now many users prepare their computers for migrate to windows 11. But from Microsoft’s point of view, not all configurations are valid, so some users use alternative sources that are not always recommended.
With all this, what is attempted is to force the installation of Windows 11 on those computers on which, at least initially, the new system cannot be installed. Precisely for this reason now we are going to talk about a danger before we can find ourselves in this situation. We are telling you all this because some attackers are urging users to install a fake update to Windows 11. The big problem is that it comes with a series of malicious codes included.
East malware hidden in the update that we mentioned is in charge of steal browser data that we have in addition to our cryptocurrency portfolios. We must keep in mind that this malicious campaign is currently active. It relies on manipulating search results to prioritize a website that mimics Microsoft’s promotional page for Windows 11. All in order to deliver this fake update.
In this way, those responsible take advantage of users who rush to install Windows 11 without automatically receiving the message. This happens if the equipment does not meet certain specifications. We can affirm that this malicious website The one we told you about and offered by the fake Windows 11 is still active. What’s more, it has the official Microsoft logos and a button that invites us to download the new system to update our PC.
Avoid unofficial installations of Windows 11
What we mean by this is that if the visitor loads the malicious website through a direct connection, they will get a ISO file of the supposed system. However, this hosts the executable of a new malware focused on information theft. After a series of analyzes that have been carried out on this malicious code, it has been known that it is not similar to others detected so far. In fact, no evidence has been found that the malware has been uploaded to the Virus Total scanning platform, so it is quite new.
The file is based on Delphi programming language and it is a Windows 11 installation executable contained in the ISO image that we downloaded. When launched, it dumps a temporary file called is-PN131.tmp and creates another file that spawns a new process using the Windows CreateProcess API. This helps spawn new processes and add four malicious files. In addition, the moment assembly is capable of bypass current security solutions that we have installed.
The main capabilities of this malware include the collection of browser cookies and stored credentials. Besides, collects cryptocurrency wallet data and file system data. This is something you can do in Chrome, Edge, Brave, Opera, or Vivaldi, among others. It is also important to know that all stolen data is copied via a PowerShell command to a temporary directory. They are then encrypted and sent to a remote server controlled by the attacker.
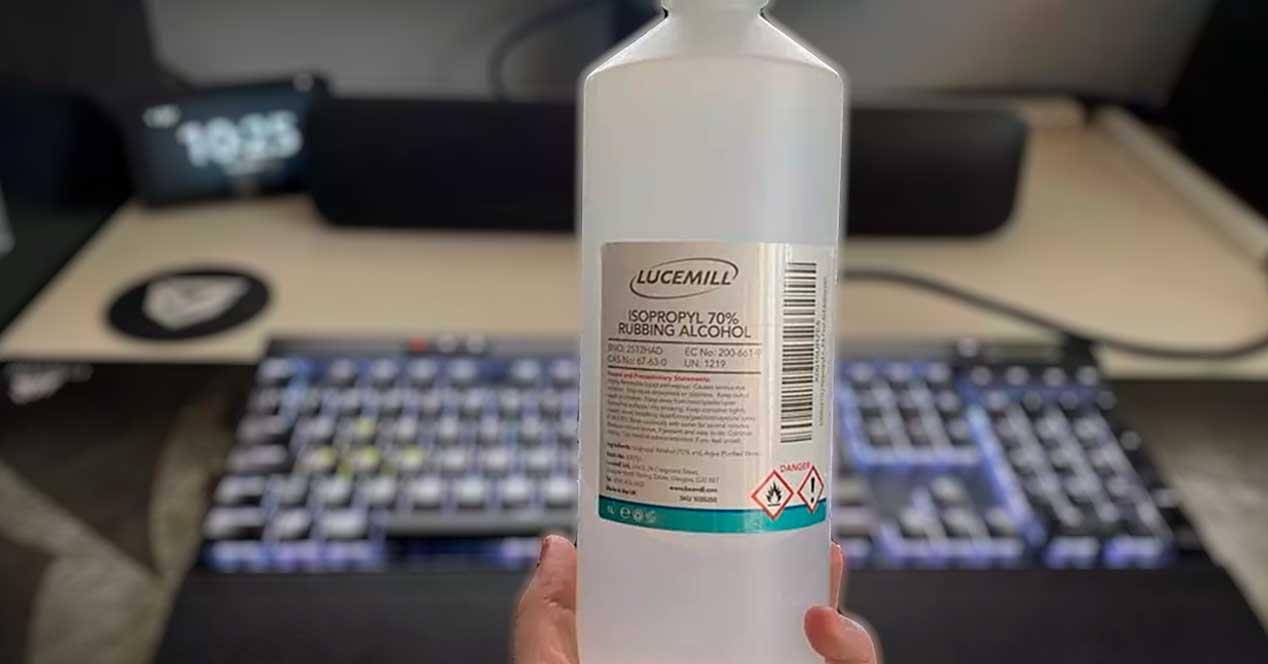
Once we know all this, it is recommended avoid downloading ISO files from unreliable sources. We must perform major updates to the operating system from within Windows itself or obtain the installation files directly from Microsoft.