And it is possible that we suspect that someone has accessed and is using our computer when we are absent. This is something that can be given both at home and in the office. It is possible that a co-worker, a roommate, our partner or anyone else may have access to the equipment without our permission. Obviously this would translate into accessing personal or confidential information stored.
It is always advisable to access the system through a password, but someone in our environment may have seen us introduce it. In the event that we have doubts, then we will see how to carry out the relevant check. In fact, we have several methods that we can use for these verification tasks, as we are going to see.
Check Windows Event Viewer
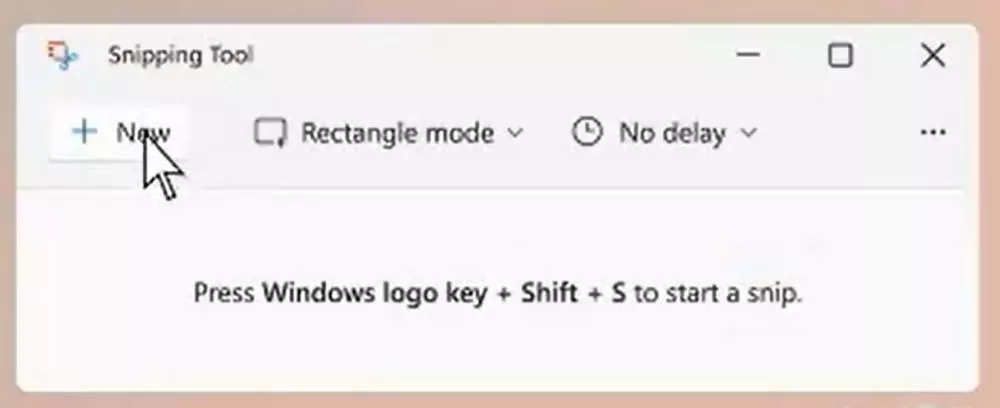
First of all, we are going to make use of a very interesting function of the Microsoft system, the Events viewer. Here all the events that are happening in Windows are stored, including the login, of course. Therefore, this is a good element that allows us to check if someone has accessed our computer without our permission. We can open this section just by writing your name in the search box from the task bar.
Next, in the left panel we place ourselves in Windows / System Logs. At that time, all the events that have occurred in the operating system will appear in the central panel of the tool. Therefore, we only have to browse through them and look for the last login to check if the time coincides, or not, with the last time we turned on the PC.
Check browser history
We can also use some tricks that allow us to perform this check. Generally, if a non-permitted user uses our equipment, it is very likely that they will make use of the Internet navigator installed. Therefore, in this case we can always take a look at the browsing history stored by it, where the last pages visited are indicated. In the event that they are not the websites that we loaded in the last session, we will have to take the appropriate measures.
View PC USB device history
Another very effective method for these tasks that we discussed is to take a look at the history of connected USB devices to our team. This allows us to check first-hand if any unfamiliar USB memory has recently been connected to our PC without our consent. To do this we are going to use the system command line.
First, we access the same typing CMD in the search box of Windows. In the new window that opens now we just have to type the following command:
reg query hklm/system/currentcontrolset/enum/usbstor /s
Take a look at recent files
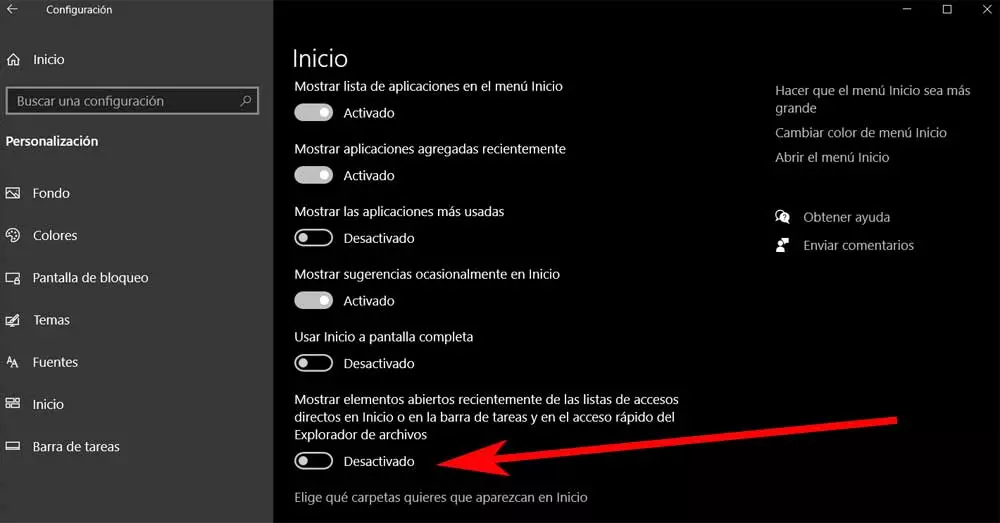
In this case and as a preventive measure, we can activate a function that helps us to check if someone has accessed our computer. In conceto we refer to the recent files that have been used, which will serve as evidence. To do this, open the application windows settings and we are in Personalization.
Next, click on the Start section and locate Show recently opened items, something that we activate. This way we will see in Start all the files that have been opened in the last sessions with the PC.