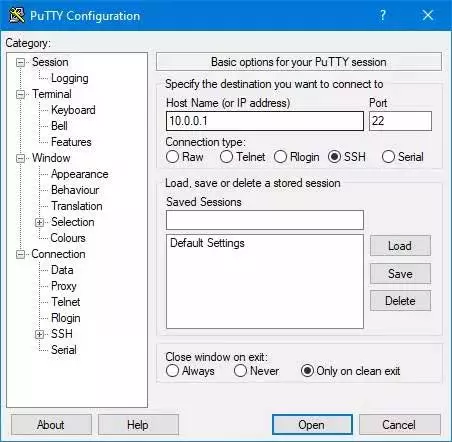
Over time, remote work with different computers has become quite common. To achieve all this we have several ways and software solutions at our fingertips. While on the one hand we have specific remote desktop programs, if we want to have more control over the connection it is preferable to use applications such as putty.
Initially, one of the main features offered by the operation of PuTTY is the possibility of connecting through protocols such as SSH, among others. Keep in mind that we find free open source software specially developed to make it easier for us to use the SSH protocol in Windows. We must know that the Redmond system has its own client to use from CMD. But here we will have a complete client with all kinds of options, both basic and advanced.
When starting the application as such, we are faced with a basic user interface that is functional at the same time. But aside from all the functionality, the external aspect of this specific application, as you can imagine, security and privacy are key elements. That is why here we are going to talk about the security features that PuTTY supports in order to protect our remote connections.
The first thing we should know in this regard is that the application, from its inception, has always had support for the SSH-1 security protocol. However, over the years this has become more insecure, so whenever possible it is recommended to use here SSH-2. Precisely for all this, the developers of the software solution implemented support for the aforementioned SSH-2 starting with version 0.50.
Other secure functions offered by PuTTY
To all this, we must add that, when connecting remotely with other equipment, the public key authentication both RSA and DSA using SSH-2, is completely new as of version 0.52. Keep in mind that when talking about the SSH or Secure Shell protocol, it is responsible for offering secure remote access. The main feature of this is that all information is encrypted.
But that’s not all, since the program also makes use of DSA or Digital Signature Algorithm to secure remote connections. Here it is interesting to know that DSA is vulnerable if it is poorly implemented using random numbers. However, based on some reports received by the developers of the application, they improved the use of it. One of the measures implemented in this regard was dispense with random numbers to secure connections. at the same time integrates other protection methods such as ECDSAwhich uses the same defense as DSA, but with more secure features.
It is important to know that PuTTY leaves system registry entries, something that can become a problem if we use a public PC. Therefore, in this case it is important to clean this hidden information when you close the session. This is something that we can do automatically by running the following command:
putty -cleanup
This removes the settings of the user who is currently logged in so that it can be accessible by others.