When we proceed to download any file from the Internet and save it to an NTFS drive, Windows add specific metadata to these downloads and are considered as attachments. When trying to open or run a downloaded file, we get the warning “The file originates from an unknown source and may be a security threat.” This prevents us from opening them directly, considering it as insecure.
This metadata added as an attachment to the downloaded item is known as zone information, which is nothing more than an invisible file stored together with the downloaded file in the form of an alternate data stream, being stored in the same location. When the file is opened, the information of the attached area is stored in the same location and verifies if it comes from outside, preventing it from being downloaded.
To try to fix it, we must configure the Attachment Manager well. We must also make sure that it is not an action derived from Windows Defender, thereby preventing any file from being downloaded. Likewise, from the Windows Registry Editor or Group Policy Editor it is possible to disable their blocking to solve the problem.
Check Windows Defender
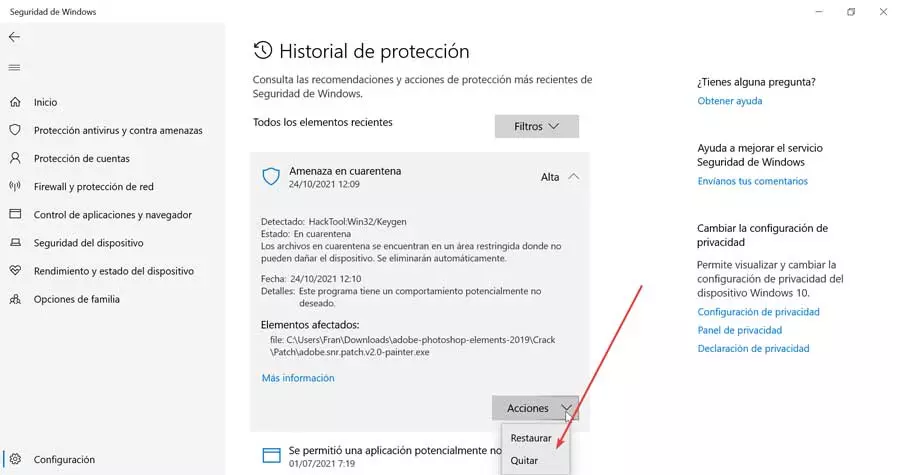
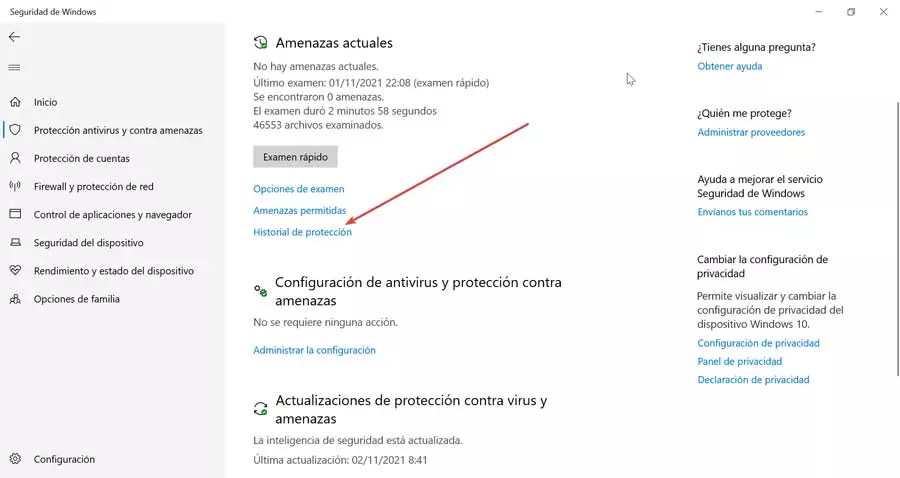
First of all, we must check if the Microsoft security tool has been in charge of blocking the downloadas it may have detected the presence of a virus. To check this, we must open the Windows Defender Security Center, from the Settings section, which we access by pressing “Windows + I”. Later we click on “Update and security” and “Windows Security”. Now on the right side we select “Windows Security”.
In the new window we select the option “Antivirus and threat protection” in the menu on the left. Now on the right side we see the option “Protection history”. Here, although the antivirus tells us that it has not detected any threat, there may be braking the discharge of some file to quarantine it.
By clicking on the «Protection history» we can see the threats in quarantine, where we will see the file record that has been detected as a virus or threat. This is not easy to detect as, although the file name is displayed, it is displayed with a temporary name. Therefore, we can delete file records that are in quarantine and we try the download again. If a new record appears in the quarantine, we will know for sure that Windows Defender has blocked it.
In this case, if we are sure that it is a false positive, then it will be necessary to temporarily deactivate the antivirus to download the file, or to restore it from quarantine so that we can have it available for use.
Configure Attachment Manager
Microsoft’s operating system has a security feature that prevents us from open items that may be considered unsafe, either from the Internet or attached to an email. In this case, it blocks it and shows us a warning message “The file originates from an unknown source and may be a security threat.” The File Manager will classify them based on the type and extension of the file.
It is possible to open a blocked download by right-clicking on the downloaded file and selecting “Properties” from the context menu. Within the “General” tab, we click on “Unlock” and finally click on “Apply” and “OK” to save the changes. In the event that we download many files, this process can be cumbersome and heavy.
For this reason, it is possible to prevent Windows from preventing us from opening files by configuring the administrator manually either through the “Local Group Policy Editor” or through the “System Registry Editor”.
Using the Group Policy Editor
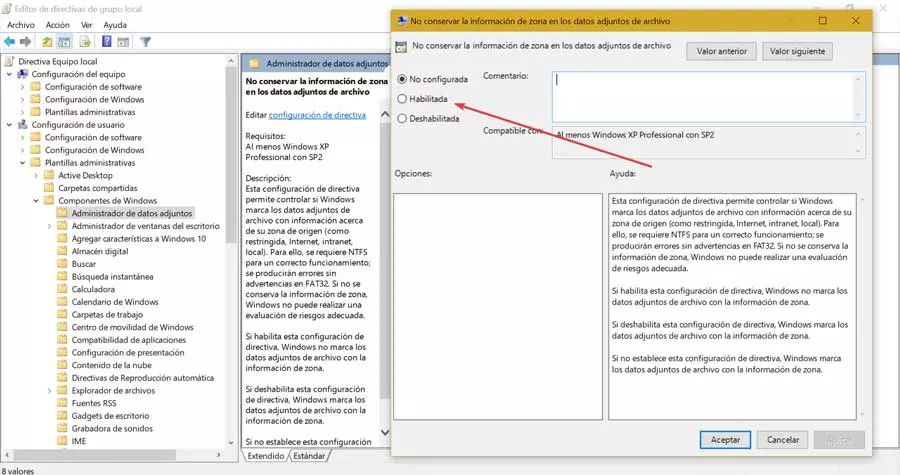
The Local Group Policy Editor is a feature that is available within Windows 10 Pro and Enterprise versions. To access it, press the keyboard shortcut “Windows + R” and the Run command will be launched. Here we write gpedit.msc and press Enter.
Next, we must navigate to the following route:
Configuración de usuario / Plantillas administrativas / Componentes de Windows / Administrador de archivos adjuntos
Later in the right panel we must double click on the policy «Do not keep zone information in file attachments». This will bring up a new window where we can choose whether or not the Attachment Manager should keep the zone information. Clicking on “Enabled” ensures that Windows does not block these items every time we open it. Finally, we click “Apply” and “OK” to save the changes made and restart the PC so that they are applied correctly.
From the Registry
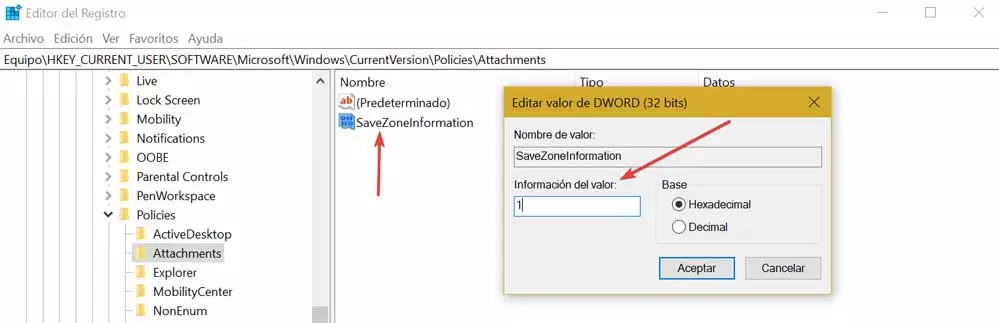
The Windows Registry Editor will also allow us to configure the Attachment Manager so that it does not block downloads. To access it, we must press the “Windows + R” shortcut that will launch the Execute command. Here, we write regedit and press Enter.
Once in the Editor, we will proceed to make a backup copy of it, in case something goes wrong. To do this, click on «File» and «Export». We must know that any bad change made can cause stability problems in the system so we must use it under the responsibility of each user. Next, we are going to access the following path:
HKEY_CURRENT_USER / Software / Microsoft / Windows / CurrentVersion / Policies / Attachments
In the event that the “Attachments” key is not found within “Policies” we must create it. To do this, we right-click on «Policies», then on «New» and «Password». When creating a new key we will give it the name “Attachments”.
Next, we right click on the “Attachments” key, select “New” and “DWORD Value (32 bits)”. We set the name of SaveZoneInformation for this new DWORD value and hit Enter.
Finally, we double click on the «SaveZoneInformation» value that we have created and change its data from value to 1 to disable Windows Attachment Manager. We click OK to finish and close the Editor. Now we only have to restart the PC and any file that we download will no longer attach zone information to the alternative data stream of the file, which will allow us to open them without problem.