The incident that OVH encountered on October 13 was caused by improper handling in a network reconfiguration. This modification was decided to respond to an increasingly significant problem on the web: DDOS attacks.
It is human error, damaging for many websites in France, which has unintentionally brought the DDOS attacks back to the fore. This Wednesday, October 13, the host OVHCloud was momentarily in difficulty. Bad luck for the French company, the incident, which has since been resolved, occurred two days before its IPO.
The origin of this incident, which made a small part of the French web unavailable and which was detailed by Octave Klaba, the founder of OVHCloud, actually comes from improper handling during a reconfiguration of the network associated with the center. company data center based in Vint Hill, on the east coast of the United States. The intervention aimed to consolidate the centre’s capacities in the face of DDOS attacks.
On the day of the dysfunction, Octave Klaba remarked than ” in recent days, the intensity of DDOS attacks has increased significantly. We have decided to increase our DDOS processing capacity by adding new infrastructure in our data center in Vint Hill (US-EST). Incorrect router configuration caused the network to go down. “
What is a DDOS attack?
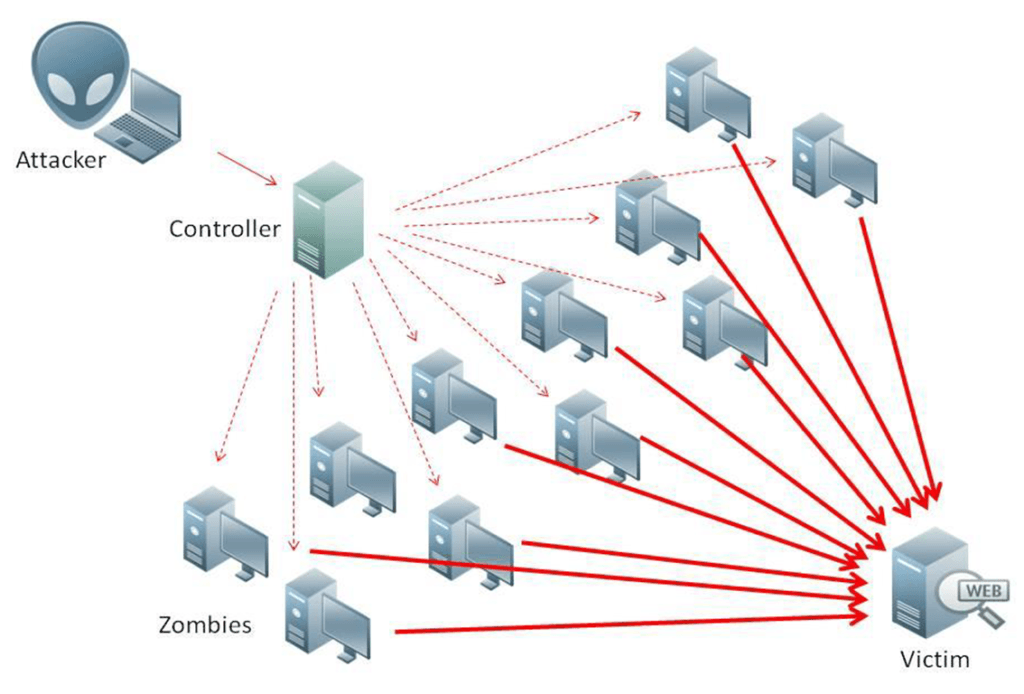
For those who are not familiar with the jargon used in the world of networks, a DDOS attack is a Distributed Denial of Service attack. The operation consists in overwhelming a server with an incredible number of requests, so that it is no longer able to process them. Normal requests suffer as a result, because they get caught up in this tsunami.
CC Nasanbuyn
There are countermeasures to contain DDOS attacks or to redirect them elsewhere (in addition to police intervention), to avoid giving the impression that the sites hosted by the targeted server are down. – whereas they are above all inaccessible due to the provider’s inability to absorb such a sudden wave of connections. But these countermeasures sometimes require the purchase of more or less expensive services.
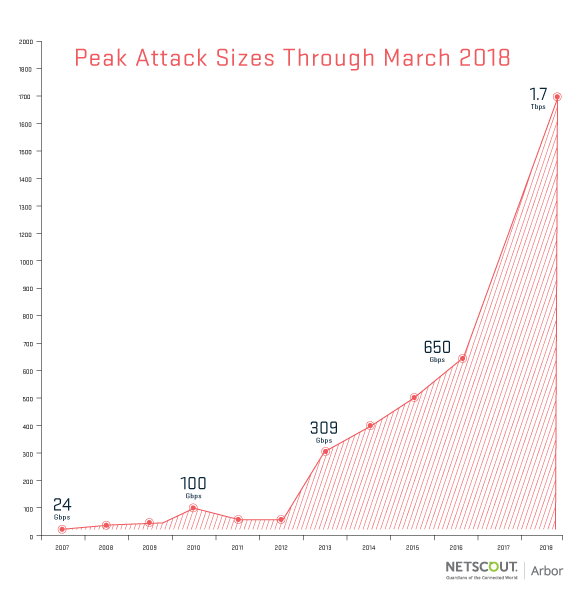
The scale of DDOS attacks is diverse, depending on the target being considered, the technique used and the entity behind it. But sometimes records fall. We remember that in 2018, the GitHub platform, specializing in IT development projects, had taken a slap at 1.3 terabits per second (Tbps). The record quickly fell the same year, with a breaking wave measured at 1.7 Tbps.
The intensity of DDOS attacks hits the roof
Today, the levels of some attacks are becoming absurd. In 2020, Amazon said it peaked at 2.3 Tbps in February 2020. And these days, Microsoft has said it hit a groundswell of 2.4 Tbps. The number one place – at least, in terms of the attacks made public – will remain a priori held by Google, with a DDOS recorded in 2017 at 2.57 Tbps.
For Microsoft, this attack is the most important ever recorded by it. It happened at the end of August. According to the American company, the target of the attack as being an Azure customer in Europe, without further details. What the company has been careful to make clear, however, is that its facilities have withstood the shock. Azure thus did not fall into the harbor.
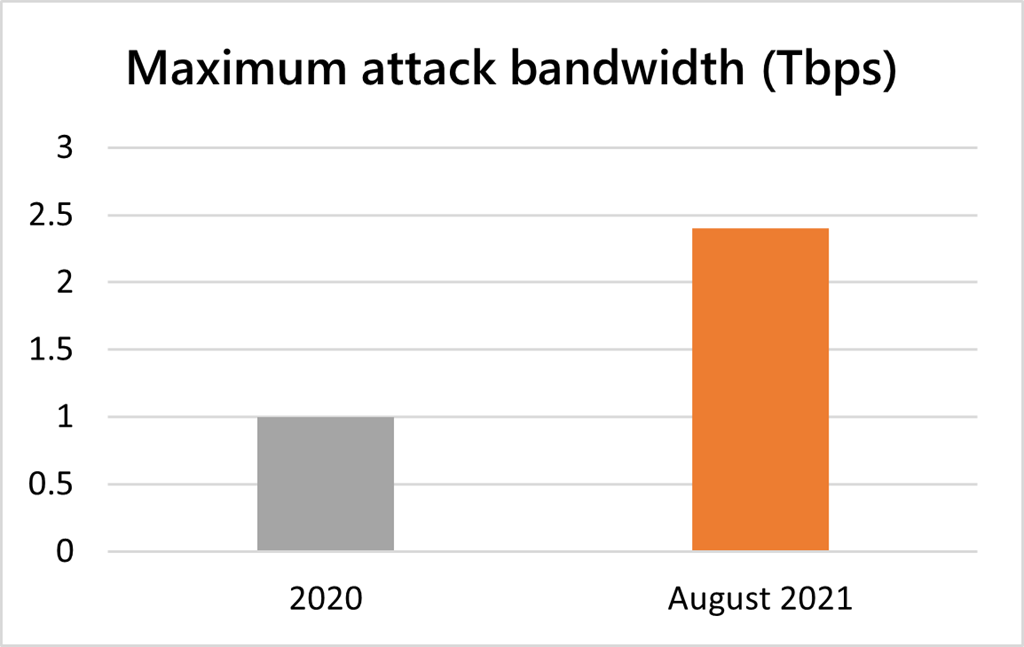
The DDOS attack, Microsoft added, unfolded in three short waves in a ten-minute window of action. The first was the most brutal, with the peak at 2.4 Tbps. The other two were lower, at 0.55 Tbps and 1.7 Tbps – “lower”, all things considered. They are still tremors of rare intensity, which many could not digest.
The attack was carried out using a botnet of around 70,000 machines located mostly in the Asia-Pacific region, such as Malaysia, Vietnam, Taiwan, Japan and China, as well as in the United States. United. The company specifies that UDP thinking was the vector of the attack. UDP (User Datagram Protocol) is a popular Internet communication protocol for conducting DDOS attacks.
DDOS attacks keep on growing
If Octave Klaba suggests that the intensity of DDOS attacks is exploding these days, the concern he describes is much more global and continues to grow from year to year. ” The era of terabit attacks is upon us “, Warned Arbor Networks in 2018 when the attack took place at 1.7 Tbps. On that occasion, the company shared a chart showing the various records it had set over the years.
This observation is shared by various players in the world of networks. ” We reported a 25% increase in the number of attacks compared to the fourth quarter of 2020 Microsoft observes in its report of the 2.4 Tbps attack. That said, he notes ” a decrease in the maximum rate of attacks, which fell from 1 Tbps in the third quarter of 2020 to 625 Mbps in the first half of 2021 “.
There is no shortage of examples of attacks and the targets are very diverse. It could be a video game publisher like Blizzard, which offers titles like World of warcraft and Overwatch, a service provider used by press sites or another used even more widely (by Twitter, Netflix, PayPal, Spotify, PlayStation Network, etc.). These attacks use zombie machines, unbeknownst to their owners, including smartphones or surveillance cameras.
A similar observation was made at the beginning of the year by the French center for monitoring, alerting and responding to computer attacks (CERT-FR), which depends on the National Agency for the Security of Information Systems (ANSSI ), a structure that acts as the state’s cyber-bodyguard. It is mentioned ” an increase in threats of denial of service attacks For extortion purposes.
Another important lookout is Cloudflare. The American company specializing in providing solutions for sites (it sells services to guard against DDOS attacks and to collect connection peaks, but also tools to optimize pages, detect intrusions or protect the web. ‘IP address) has noted an increase in DDOS attacks.
In a stage shared in July 2021, everything is on the rise or almost and there is, in the light of the various testimonies, no tangible sign allowing to hope for a pause or a lull in this area. So much so that today, according to Cloudflare, DDOS attacks have passed over time ” from the status of background noise to that of a major problem affecting our daily life. “



