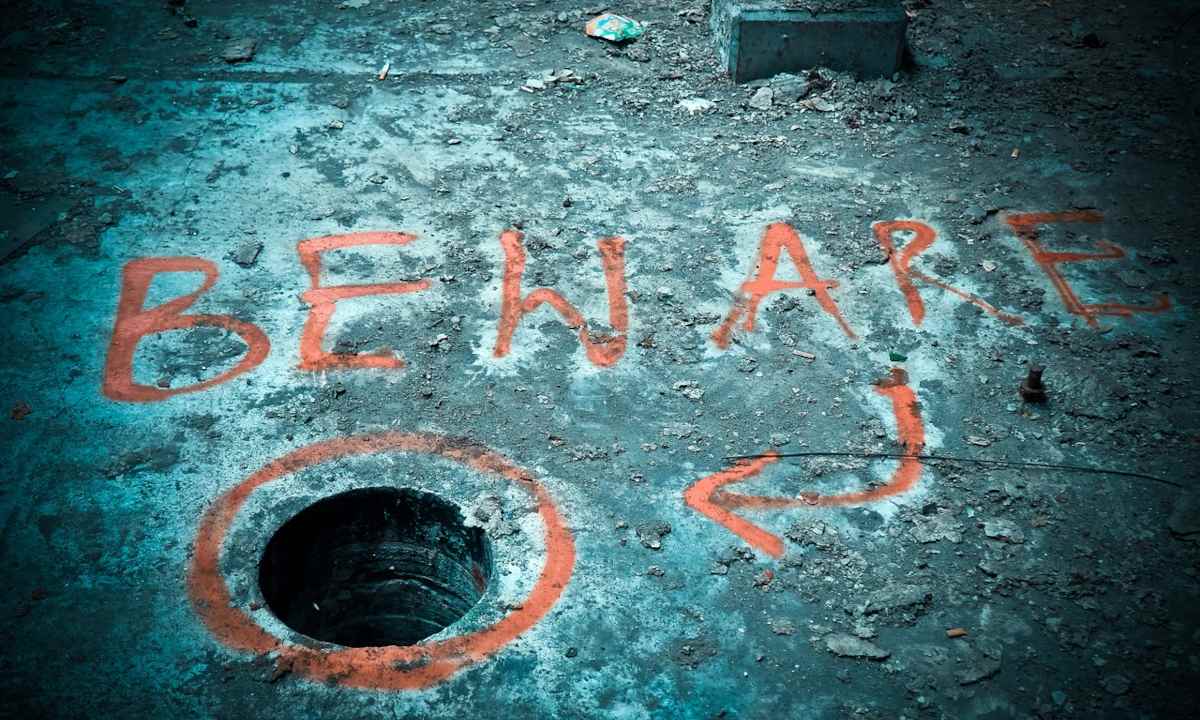
If you do not live in a cave and you are up to date with technological information, it is more than possible that you have already come across the news of a vulnerability that affects almost any Linux distribution and that had been there for more than twelve years, without anyone knowing about it; a very simple vulnerability to exploit according to the researchers who have discovered it, thanks to which an attacker could perpetrate an escalation of privileges and gain administrator permissions.
If you haven’t heard yet, relax, because the almost all major distros have already issued the patch that closes the hole. As long as you have your system updates up to date, you’re covered.
But what does that vulnerability consist of, you ask? What component is affected? Is about pkexec, one of the PolicyKit tools used to run applications with administrator privileges. PolicyKit, now Polkit, is the standard component for managing privileged processes on Linux systems. In any case, it is not a part of the Linux kernel as such, hence the talk of Linux distributions.
All the information related to this discovery is in this article by Qualys, a company that has discovered and warned about the bug. In fact, all the information is there, except a viable method to exploit the hole, since they are waiting for the main distributions to have released their patches.
The curious thing about the case is that the vulnerability is old, yes, but… was it undiscovered? Well, no: the error was not only present in the pkexec code practically from its first version, that is, since the tool saw the light, but also there is an independent developer who sounded the alarm in 2013even sending a patch that, apparently, was never integrated.
Lol, I blogged about this polkit vulnerability in 2013: https://t.co/a6ciqwCmyt. I failed to find an actual avenue for exploitation, but did identify the root cause.
— Ryan Mallon (@ryiron) January 26, 2022
The only thing the guy didn’t get was a viable way to exploit the hole; Or in other words, all software has bugs, but it is only when those bugs pose a security risk that they are called vulnerabilities. The question in this specific case is if someone discovered the problem before and kept it quiet.
Namely; but I am going to take advantage of the time to respond to a question, or perhaps a reproach, that you throw at us from time to time, coinciding with news like this, that in MuyLinux we usually pass by. Well, it’s not about “hiding” the problems of Linux, far from it: it’s about the fact that all software is susceptible to this kind of problem and it’s very boring information to cover, especially when there is no risk, but rather it only serves to write flashy headlines that only confuse.
And as an example, a button: the same one that concerns us, because as it happens with 99% of these vulnerabilities, this cannot be exploited remotely, but requires physical access to the computer. If you add to that the news comes out of the hand of the patch, that’s why we only pick up this news from time to time.
Image: Pixabay



