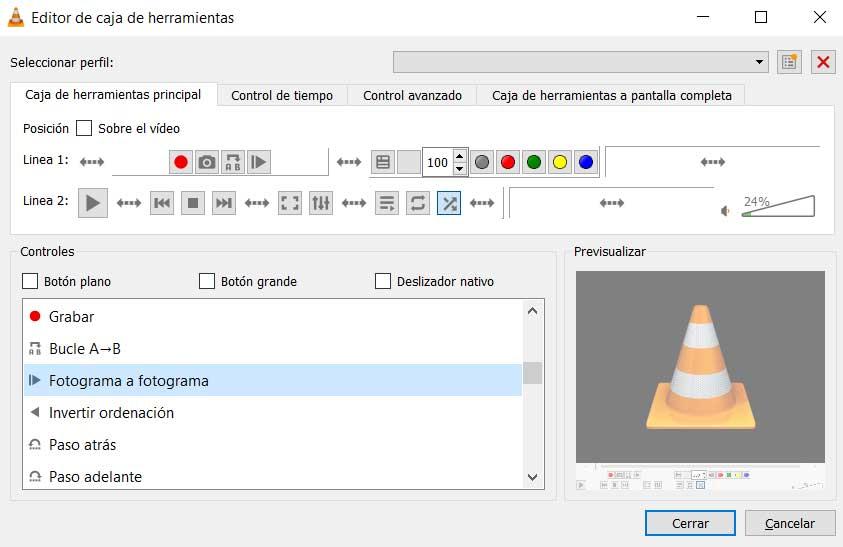
Over time, the amount of personal data that we store and use on our computers is increasing. Hence, we must take care of the security provided by the programs we install so that there are no leaks or security flaws, as has happened now with VLC.
Surely many of you already know that here we refer to one of the most loved and used multimedia players in the world. This is a product that has gained the trust of most over the years and we find it on most desktops and mobile devices. However, from what we have now learned, some security researchers have discovered a malicious campaign that directly affects this software.
Specifically, we mean that a series of hackers associated with the Chinese government are using VLC to launch a custom malware loader. At first, everything indicates that this is for espionage purposes. We say this because it initially targets various entities related to government, legal, and religious activities. Similarly, traces of attacks via the app have been seen on non-governmental organizations on at least three continents.
It is worth mentioning that the malicious activity has been attributed to a well-known group calling themselves Cicada. We talk about a attacker that in the past it has already used other names and that it has been active since last year 2006. At the same time it is interesting to know that the first movements in this sense were detected in the middle of last year 2021, but it has remained active until today.
VLC, victim of espionage malware
To give us an idea of all this, there is evidence that the initial access to some of the compromised networks was made through a Microsoft Exchange server. Later, experts from the security company Symantec discovered that, after gaining that access, the attacker deployed a custom charger in other systems committed to the help of the mentioned VLC.
As has now been discovered, the attacker uses a clean version of the popular media player. It includes a malicious DLL file stored in the same path as the media player’s export functions. This is a technique known as loading side of dll and it is widely used to load malware into legitimate processes and hide malicious activity. In addition to the custom loader that we mentioned, a WinVNC server is also displayed. With this it is achieved gain remote control of systems of the affected victims.
In turn, this same attacker that we are discussing uses a tool that is believed to be proprietary, Sodamaster, and has been used since at least the past year 2020. It runs in the system memory and is equipped to evade detection by the attacker. security software installed. The entire malicious set is also prepared to collect a large amount of information from the affected computer. We talk about data of the importance of the operating system or the running processes. As well as downloading and executing various dangerous payloads from the control server.