There are many types of attacks that can reach us from the Internet through different pathways. Some more dangerous than others, but in most cases we try to avoid them at all costs. Likewise, there are scams that focus on fear, as we are going to tell you about now.
And it is that at the moment a dangerous campaign is being detected that is affecting a large number of users. It wants to focus on fear and threats to make us fall into the trap and rob us, it’s that easy.
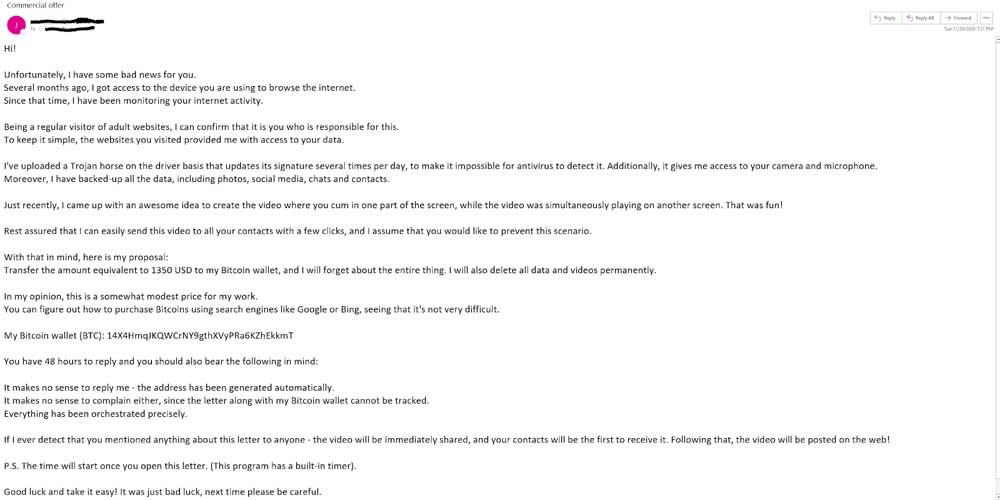
The way it works seems simple, but it seems to be quite successful from the point of view of attackers. Specifically, they send a mass email to potential victims with the following attached message “I am a hacker and I gained access to your operating system”. In addition, in the same body of the email we are informed that they have been monitoring us in recent months to achieve the objective mentioned here.
Let’s start from the fact that we are working with an increasing amount of sensitive and private information on our computers, both mobile and desktop. Hence, both our phones and computers are increasingly linked to our personal lives. This is precisely what the attackers want to take advantage of in this campaign that we mentioned to you through the email that they sent us. Perhaps if you are experienced users in the world of technology you will directly discard it, but this does not extend to all cases.
How to avoid these fear-focused scams
As you can imagine, these scams are based on emails that try to convince victims that a cybercriminal has taken control of your system. All this means that they have been watching them through their cameras and have a large number of personal images. To keep your privacy safe, these attackers ask for a certain amount of money to be paid.
So they take advantage of the uncertainty, fear or ignorance of the victim. All this to avoid embarrassment and being exposed. This is a recent campaign detected and reported by the security company Avast. Likewise, this company wants to reassure those affected, since these emails are false and fictitious, hence they should be treated like any other phishing scam of the many that we receive daily.
It is true that this format of scams has existed for a long time. But this recent campaign that comes to us by email is more elaborate and seems more credible. That is precisely where its danger lies, although as we tell you, it is nothing more than another phishing campaign, so we should not believe anything the message tells us. One of the proofs of this is that no more data is specified, such as the accounts that have been accessed, the operating system type, leaked information, etc. In other words, it can be considered as too generic a threat.
One of the main objectives of this email is that, upon receiving it, we first act and then think about it. Well, we must do the opposite. First of all, analyze the message as such and surely we will conclude that it is false. In the event that we receive an email of these characteristics, the first thing is to be wary. From there we can carry out some preventive actions such as changing the passwords of the most private platforms, update all our softwareor use systems two factor authentication.