Microsoft has established security as one of the highest priorities of Windows 11, a policy that, in addition to providing benefits, has also led to certain critical situations around planned obsolescence. Despite this, the Redmond giant is willing to continue in the same direction, so it has updated Windows 11 22H2 so you can make use of the Total Memory Multi-Key Encryption (TME-MK) implemented in Intel’s Alder Lake (12th generation) processors, a technology that is focused on virtual machines.
As Microsoft explains, TME-MK offers “hardware accelerated encryption of DRAM”. This is not a feature exclusive to Intel’s twelfth-generation consumer-oriented processors, as it was previously implemented in third-generation server-oriented Xeon processors. This means that “Azure, Azure Stack HCI, and now Windows 11 22H2 operating systems also take advantage of this next-generation hardware feature.”
The use of encryption as a security measure will continue to be important to the company, especially considering that it has been “for a long time an established mechanism to keep data out of the reach of prying eyes. By encrypting data while at rest, in transit, and in use, we can prevent unexpected third parties from gaining access to sensitive information for the life of the data”.
Microsoft reminds that data at rest is protected with disk encryption technologies, while protocols such as SSL, TLS and HTTPS are used for data in transit. In recent years, various technologies have appeared aimed at protecting data in use through hardware, which are used in Azure and are capable of providing an end-to-end encryption scheme. Using the data protection built into the hardware of personal computers is one of the reasons for the high requirements of Windows 11 and it is something that is being implemented in Linux as well, although for now as an option and not as an imposition.
Another aspect remembered by the Redmond-based corporation is the introduction of Bitlocker in Windows 10, which provides encryption of the data present on the data storage unit in order to prevent it from ending up in the hands of a thief who has stolen a laptop. Mentioned this, we take the opportunity to recommend from MuyComputer the use of disk encryption at least in laptops that leave home regardless of the operating system, be it Windows, Linux or macOS.
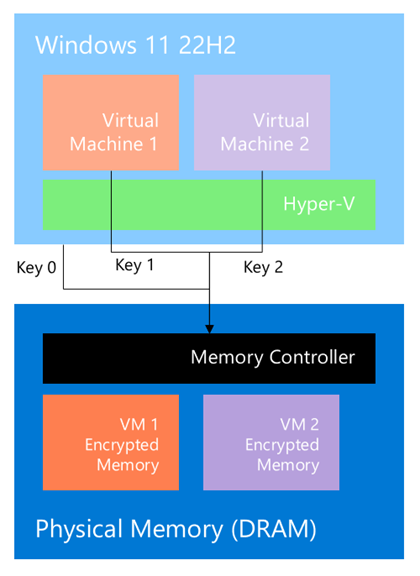
On the other hand, hackers have researched over the years to be able, for example, to carry out attacks against physical components with which they can recover data from media such as RAM. This is where features like TME-MK, which relies on hardware acceleration capabilities for a controller to encrypt data before it is sent to DIMMs and decrypt it when it needs to be processed.
“Memory controller-based encryption prevents attackers who have physical access to DRAM from being able to read the plaintext memory contents. TME-MK extends that paradigm by allowing different virtual machines (partitions) to have unique memory encryption keys.”
In short, Microsoft gives another twist to the security of Windows 11 22H2 with the implementation of TME-MK. This should come as no surprise to those who have closely followed the system’s trajectory and who understand the security mechanisms that have been introduced into motherboards and processors in recent years.