Differences between hacker and cyber criminal
To understand better what is a gray hat hacker, it is convenient to know exactly what hacker and cybercriminal mean. Sometimes the terms can be confused, although it is a mistake. They do not act in the same way, nor do they have the same objectives. In fact, we can say that network security is sometimes a struggle between the two.
A hacker He is an expert in computer security who is responsible for putting his knowledge into practice for the common good. For example, analyze a system to find vulnerabilities that can be exploited, determine if a Wi-Fi network is protected or not, etc. There are times when even large corporations like Facebook hire hackers to help improve security.
In this case, this person or group of people are going to put themselves in the shoes of a Hacker, but they are not going to do anything really bad. If, for example, they detect a security flaw in an application, they are not going to exploit it to steal data or put everyone who uses that software at risk.
On the other hand, a cybercriminal or hacker is also going to have big skills and knowledge computer security, but will use them for evil. They are going to look for how to steal passwords, how to bypass the protection of a system or what to do to cause a malfunction in a server.
Hackers are responsible for creating and executing malicious code, sneaking viruses onto victims’ computers, and ultimately creating problems for everyone. That is why we say that it is a fight between the two, since the first one to detect a bug will achieve its objective, which can be to solve it or exploit it for its own benefit.
How a gray hat hacker acts
So what does a gray hat hacker do? We can say that it is a kind of hybrid between a hacker or white hat hacker and a cyber criminal. But even so, there are some points that must be highlighted to really know what its objective is and how it can or cannot affect everyone’s safety.
A gray hat hacker is characterized by break the law. That is to say, it is going to carry out different types of illegal practices. Of course, it should be noted that they do not act as a hacker. They are not with bad intentions, nor are they going to affect a third party in a negative way, such as stealing passwords, for example.
basically intentions are good, they will carry out different types of strategies to warn of possible vulnerabilities or dangers that exist in a system or any computer program. They will also perform different penetration tests, research or use tools to break the security of a computer and gain access.
Therefore, the main characteristic or difference is that a gray hat hacker is going to break the law to carry out his actions. For example, they will enter a company network without permission, if only to later warn that there is something wrong that they must correct.
Also known as Gray Hat and, in short, they have the same objective as a hacker but in this case they will not take into account the current legislation. We can say that they commit crimes, although they are different from those of a hacker who would act for his own benefit and be able to steal access codes or information of any kind.
Another difference is that white hat hackers do not always notify companies first if they detect a vulnerability. Sometimes they can also share that information with the community of cybersecurity experts, even if they do not act and simply observe.
Key differences with a hacker
Gray hat hacker and computer hacker are not the same, as you have seen. Nor is it if we compare it with an ethical hacker. We will briefly show how it differs from a cyber criminal. This way you will have a clearer idea of how each one works. Therefore, these are the key differences what you should know:
- Does not seek evil, such as stealing data or passwords
- You will inform others of the problem and not use it for your own benefit
- It breaks the law, but not to really harm a company or organization
- Detect vulnerabilities to correct them, not to exploit them
Why are hackers necessary?
After having seen what a gray hat hacker is all about, you may be wondering What are hackers for in general? and whether or not they are necessary. The truth is that yes, they are very useful to safeguard computer security and protect web pages or any service that we use on the network.
Its mission is to detect vulnerabilities that may appear. It must be taken into account that there are many security issues when using computer programs or any service on the Internet. For example, flaws that allow an intruder to access sensitive information or can steal exposed passwords.
A hacker is going to get ahead of a cybercriminal. Will spot those bugs and notify the responsible company so that they can correct them as soon as possible. They may even have been hired by that organization where they have found the problems, with the mission of alerting them when they see that something is not working well.
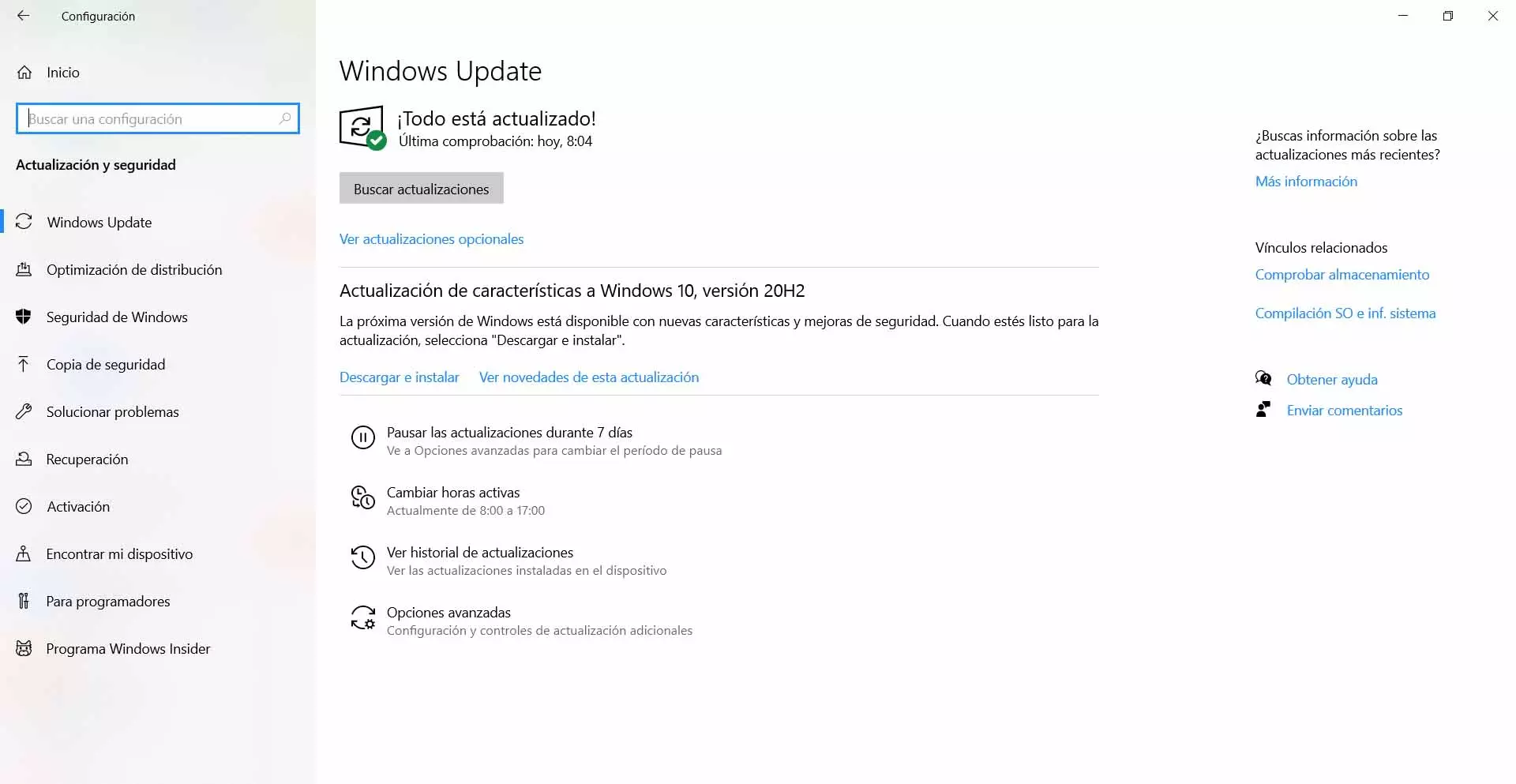
In this way security patches can be released. It is important to always have everything updated to the latest versions and in many cases this will only be possible if a hacker has previously found vulnerabilities and has reported it. This must be applied to operating systems, to any program or drivers.
Conclusions
Therefore, as you have been able to see a gray hat hacker Its mission is to investigate and detect vulnerabilities, but to do so it does not take legality into account. He differs from an ethical hacker just in what we mentioned, although he also has differences with a hacker, since in this case they seek evil.
A Gray Hat will act on its own, but once it obtains the information or detects any problem, it usually shares it with the community and not directly with the affected party. Of course, as you have seen, it is not going to steal passwords, nor is it going to try to harm a company or whoever has been affected by that failure.