What is Windows DirectAccess?
DirectAccess is a new feature built into Windows operating systems starting with version Windows 7 and Windows Server 2008 R2. This technology allows users to use the company’s network resources as if they were really there, they will be able to access network shares such as Samba servers or printers, as well as applications that run only locally, and they will even be able to access to company websites that are only allowed to be accessed on the intranet.
DirectAccess allows us to obtain all this without the need to connect to a VPN server that is in charge of tunneling all the network traffic of the different clients. If we have DirectAccess activated on our computer, all requests that require access to the intranet (web services, internal email, shared folders, network printers, etc.) are directed to the intranet directly, without using any type of VPN for communication. point to point connection.
This functionality actually establishes an authenticated and encrypted IPsec tunnel for traffic sent to a DirectAccess server, but we don’t have to configure any kind of advanced parameters to connect. This DirectAccess server is the one that acts as the default gateway, and it is based on IPv6 only, however, if the business network still uses networks with IPv4 there is no problem, because it allows us to make use of technologies such as 6in4, Teredo and others. , in order to properly encapsulate the traffic so that it works well.
DirectAccess allows us to establish communication with the server as soon as the computer connects to the Internet, even before the user logs in with their user account. In this way, we will always be connected to the company, without the need to run the risk of connecting to the Internet first, and then establishing the VPN tunnel, because in many cases we may forget completely. In addition, it is also really useful to get remote support from the IT department, because they will be able to access our team easily and quickly, without having to wait for the VPN tunnel to be established.
The Windows operating system allows us to route all network traffic through the internal network, and not using the default gateway in cases where we want to access the Internet from home, all traffic will go to the DirectAccess server (to the company ). Now we are going to show you how to configure this interesting functionality.
Configure internal routing via gpedit
The easiest way to configure internal DirectAccess routing is through local group policies, to do this click on the “Start” or “Windows” button and search for “gpedit.msc» and open it, it will ask us for administrator credentials. Once inside, we have to go to the section:
- Computer Configuration / Administrative Templates / Network / Network Connections
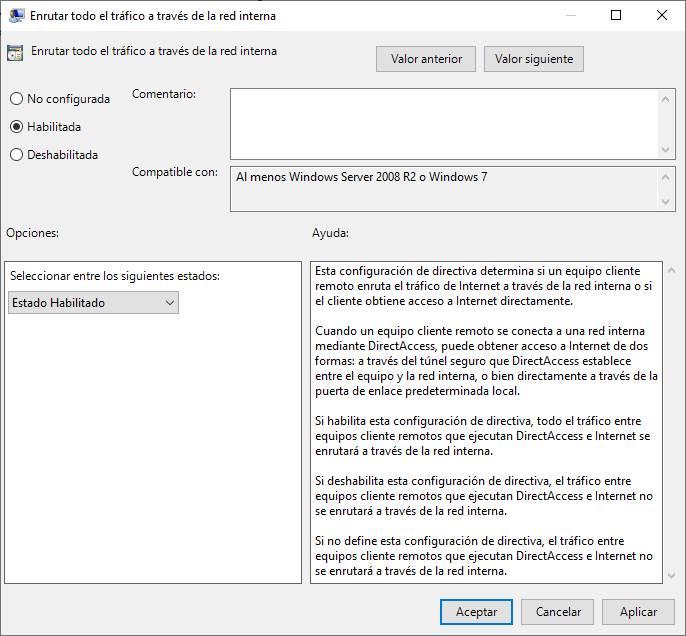
Once we are in here, we can see the different configurations available at the network level, we must choose the option «Route all traffic through the internal network«. By selecting this option, we will be able to see on the left side both the requirements and also a brief description of what makes this option so important if you use DirectAccess.
If we double click, we will have several options available:
- not configured: This is the default option, in addition, the default policy is not to use traffic routing on the internal network.
- Enabled: We will enable traffic routing on the internal network.
- disabled: we disable traffic routing on the internal network.
Enable this option
If you are interested in enabling this option, in the following screenshot you can see both the description of this option, as well as the different states that we can select. What we have to do is click on «Enabled» and then on «OK».
Once selected, click on “OK” and proceed to restart our computer to apply the changes correctly and start working with network routing to the internal network with DirectAccess. In this way, we will not use the default gateway for Internet access.
disable this option
In case you want to disable this option, we have two options. The first option is to go back into this same configuration menu and proceed to select “Not configured”, click on accept and restart the computer so that the changes are applied. The second option is to go back to this same configuration menu and choose “Disabled”, click accept and restart the computer again.
Either of the two options is perfectly valid because the “Not configured” option has this option disabled, that is, it is not activated by default in the Windows operating system.
Once we know how to enable and disable this option using the local group policy editor, we are going to teach you how to do it through the Windows registry.
Configure it through the Windows registry
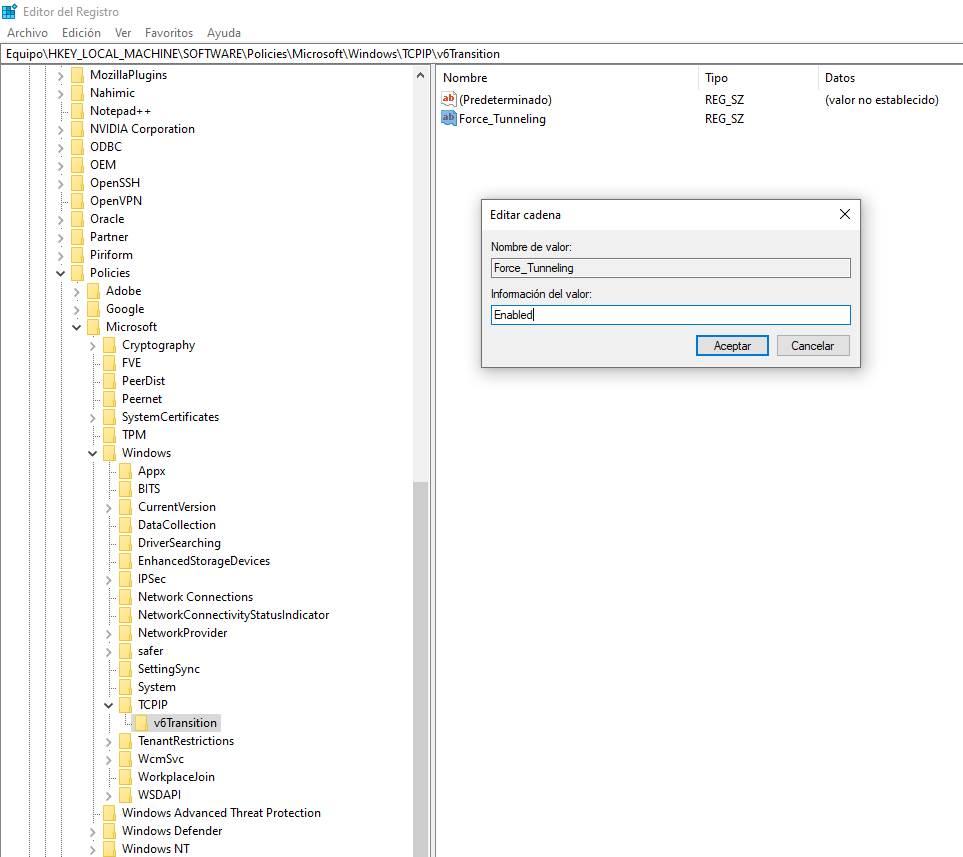
If you want to do this same configuration through the Windows registry, you must click on “Start” or “Windows” and put “regedit”. We open the registry with administrator permissions, and proceed to go to the following key:
- HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftWindows
Once we are in this key directory, we need to create a new key. Right-click on “New > Password” and give it the name “TCPIP”. We get into this new key called TCPIP and proceed to create another new key «New > Key» and we give it the name «v6Transition». Once we have created this new key, we go inside and create a new string “New > String” and name it “Force_Tunneling«.
Once we’ve created the Force_Tunneling string, if we double-click or edit the string, we can put in two values:
- Enabled: Will enable routing of all traffic to the internal network.
- Disabled – Disables routing of all traffic to the internal network.
Another option you have to disable this functionality is to delete the chain that we have created, and it will automatically stop working. You must remember that you have to restart the computer or server for the changes to be applied correctly.
As you have seen, if you are using DirectAccess and you want to route all network traffic through the internal network, this configuration is essential so as not to send the traffic to the usual default gateway that you have configured.