One of the things that most concerns Internet users and companies is security. We are increasingly aware that we must maintain a good cybersecurity policy. One of the most pressing threats businesses must address right now is when they have poor security. In this case, they are more exposed to attacks from ransomware, Phishing and other types of malware. The reason we are not aware is due to lack of cybersecurity training and misinformation. Another danger is also some common cybersecurity misconceptions that put organizations at risk. In this article we are going to show cybersecurity myths that compromise your data and information that you thought were true and are not.
A worker is not responsible for safety
Today there is still a misconception that IT security is still seen as an IT team issue. Workers also have a responsibility to ensure the safety of that organization. A company’s employees represent its largest attack surface. For this reason, cybercriminals launch phishing attacks against them because they trust that their lack of security knowledge will make their attacks successful.
In that regard, if employees are careless when clicking links in emails or downloading software, they can seriously compromise a company’s security. Thus, cybersecurity education is very important, and training courses must be offered continuously over time to employees. If we act like this, workers will be able to detect threats and act appropriately.
Attacks are not targeting small businesses
Another of the existing cybersecurity myths is that most attacks are carried out against large companies such as Google, Yahoo, Microsoft or Amazon. This comes because people think that they will be able to get larger sums of money from these big companies. However, the reality is very different, for example in the UK more than 10,000 small businesses are attacked every day. The reasons why this happens is because they have weak security procedures such as:
- Bad password usage policies.
- Failure to install updates.
- Not using necessary security software.
Small businesses, because they have a limited cybersecurity budget to fix the problem, should take advantage of the knowledge of an IT help desk. They can advise you on the most appropriate defenses for your business.
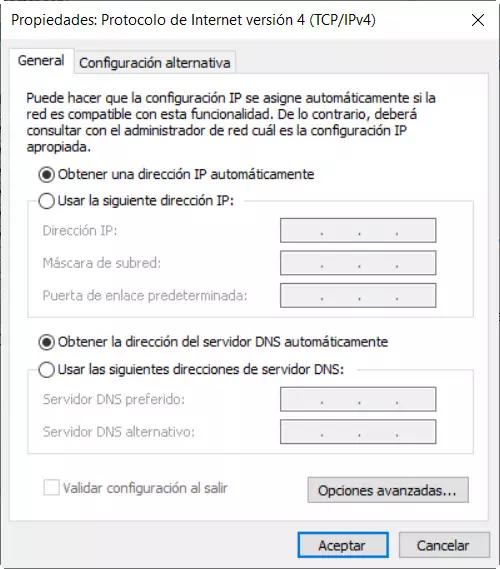
Myths about passwords and antivirus
As for passwords, there are also cybersecurity myths that are false. Some believe that adding capital letters, numbers, or special characters to their one-word password will make it impossible to crack. However, one thing that is not taken into account is its length. In that sense, with the right software, short passwords no matter how complex they are can be cracked in a matter of days. For this reason, in addition to using long passwords of 12 characters or more, it is good to have two-factor authentication activated. Thus, when we log in we will be asked to enter a security code that will be sent to the phone or a verification application such as Google Authenticator will be used.
Another belief is that a basic antivirus like Avast or McAfee will be enough to protect our company. Now, we have dedicated tools to fight against specific threats like ransomware. In that regard, we need a synchronized approach to security where all solutions interact with each other. We will also need backup and disaster recovery solutions to mitigate any incidents such as a ransomware attack.
Protecting ourselves from cybercriminals is enough
Another of the cybersecurity myths is that, by protecting ourselves from hackers, we have already complied. In addition to external threats such as cybercriminals, we also have internal ones. One could be from losing a USB stick or accidentally emailing a confidential document.
There is also the problem of disgruntled workers who have access to sensitive employee or customer information. They could then steal it or willingly share it out of revenge. To solve problems of this type we will start by blocking access to your central systems and ensuring that fewer workers have access to the company’s private and vital information. Also removable devices must be encrypted so that in case of loss we can be calmer. Finally, you have to set up your email to block certain attachments so they can’t be shared outside the company.