We always talk about the importance of having a good antivirus installed on the PC that allows us to be protected from all the threats that we can find on the network. But hackers always want to be one step ahead, and try in every way to find a way to bypass these security measures, take control of victims’ PCs, and make it as hard as possible to disinfect the system. . And, in this way, a new malware arrives that, if it infects our PC, can give us many headaches: BlackLotus.
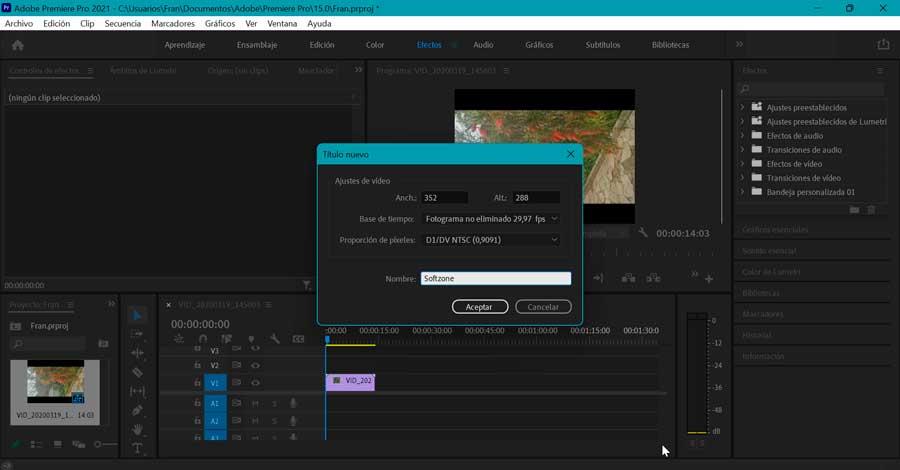
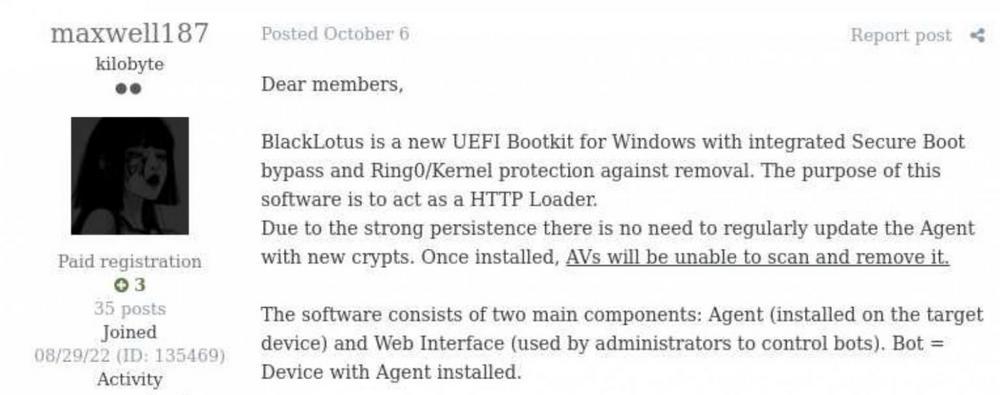
BlackLotus is a new UEFI-type malware that has just been put up for sale on specialized hacker forums. UEFI-type malware is different from what we can find in Windows. These threats are not designed to take control of an operating system as such, but rather are intended to infect the computer’s UEFI BIOS, and be able to act directly on the RAM from there.
As Windows itself is not infected, security programs are unable to detect this malware. And, meanwhile, he is able to completely control all aspects of the PC. When we turn on the computer and load the BIOS, the malware starts directly and remains running in RAM. From there you have full control over all Windows security components, such as the Hypervisor-Protected Code Integrity (HVCI), Windows Defender, and even UAC account control. It also has many features to avoid detection, such as an anti-virtual machine shield, code obfuscation, and parsing blocking. Furthermore, it manages to run on Windows with SYSTEM permissions, so no antivirus will be able to even see it from afar.
A very complex malware… and expensive
Those who want to get hold of a copy of this malware will have to pay neither more nor less than 5000 dollars. A very high price considering that, although it is an excellent backdoor for other malware, it does not do much by itself. Of course, he also comments that the new compilations of the malware will cost “only” 200 dollars.
It is very complicated to protect computers against this threat. The first thing to keep in mind is that our motherboard is still undergoing maintenance and receiving new firmware versions. In addition, it is also necessary for the manufacturer to update the bootloader to protect the system from the vulnerability used by the pirate, something that is not easy either, since there are hundreds of bootloaders.
Finally, although it is very difficult to suspect that we are infected, if we have suspicions or indications, and we want to make sure to eliminate the threat, what we must do is re-flash the UEFI BIOS on the motherboard. A process that is not suitable for everyone.
At the moment it is not known if the malware is complete or if some modules are missing. And, to find out, the only way is to get a copy of it and run it in a laboratory, something that, for now, seems complicated.
UEFI malware: a new threat to watch out for
UEFI malware has been around for many years. However, this technique was mainly limited to very small and advanced groups, such as governments or very advanced espionage companies (NSA or APT). However, as expected, sooner or later this technique has started to be used by other hacker groups, such as Trickbot.
Now, seeing how other hackers can create their new pieces of malware with relative ease, and that they are sold at a more than acceptable price to the highest bidder, this fact becomes much more worrying. Therefore, it is necessary to extreme, more than ever, the precautions.