What variety of hackers are there
Although the objectives of cybercriminals are not always the same, it should also be noted that not all are the same in terms of their origin. As we will see, some may act on their own, others in a group, others as a rental service, state hackers, hacktivists …
Pirates in charge of stealing company data
One of the types of cybercriminals that we can find are those who act to steal data from a company. They are usually hired by the competition or even on their own wanting to spy on rivals. What they basically want is to obtain a wide variety of information, such as names of workers, possible technology they use, improvements in a certain product, etc.
It is a fact that information has great value on the web. Take, for example, a company that manufactures electric cars. A competing organization may want to know more about the technology they use, when they will bring a product to market, or at what price. They can hire hackers to penetrate the network of that rival company and thus obtain as much data as possible.
State cybercriminals
This time we are dealing with cybercriminals backed by a government. Normally their mission is to attack rival countries to obtain information, paralyze companies and strategic sectors, spy and generally cause problems.
A clear example is SolarWinds, which was a series of attacks attributed to Russia and aimed at attacking different departments and organizations in the United States. But there are many similar attacks and in most cases it is never proven that they are really state-controlled cybercriminals.
As a service
Something that has grown a lot in recent times is malware As a Service or malware as a service. Where is this? Any user can hire the services of an attacker. You can pay to attack a company, organization, steal someone’s data …
Furthermore, hackers also offer their services in the form of malware. In this case, what the person who wants to attack does is buy a kit, a series of malicious files that he can then execute. For example, to introduce viruses into a company, sneak ransomware to others and encrypt files and then ask for money in return, etc.
Hacktivists
Hacktivists are cybercriminals who use hacking to claim something. For example, for political or social reasons, questioning the way a company or organization works … They can attack something in particular so that it does not work, such as leaving a company website in disuse, stealing data from a government, etc.
Normally in these cases there is usually a group behind and not just one person. They usually work together and each one of them has a different function within what that group would be.
Individual or group
Following the thread of what we mentioned, a clear difference between the different types of hackers is whether they are individual or act in groups. Here it should be noted that the objective may be the same, such as attacking a company or stealing someone’s data, but not the way in which they achieve it.
On the one hand, we are going to have a cybercriminal who acts out of his own interest, with his own resources and knowledge. On the other hand, we would be facing a group of hackers who share the different tools and also knowledge to carry out the attacks.
How to protect ourselves from hackers
We have seen that there are different types of cybercriminals. Regardless of their origin, they usually have objectives such as stealing passwords, infecting computers, spying … Therefore, we must be protected and not make mistakes that could affect us. Let’s see how to improve security.
Have safety programs
The first thing is to always have security programs. Having a good antivirus, such as Windows Defender, Avast, Bitdefender or any other, is something that will help us avoid the entry of malicious software and also to detect files that are on the computer and that we must delete.
This is something that can help us protect ourselves from hackers, be they of one kind or another, and we must apply it to any device we have.
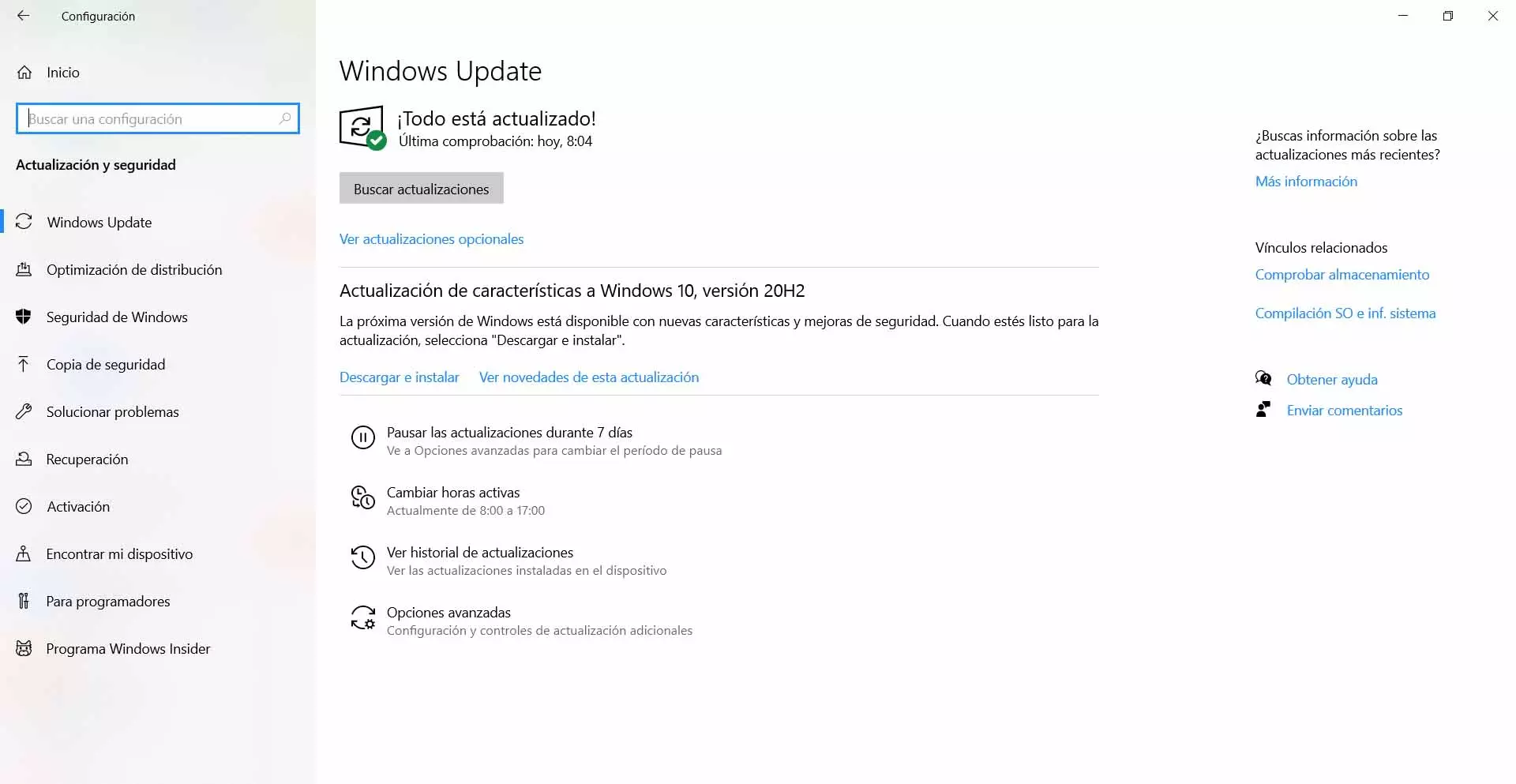
Keep everything up to date
Of course it is also essential to have everything updated correctly. Sometimes vulnerabilities can emerge that are exploited by cybercriminals to launch their attacks. Thanks to installing the patches and correcting those bugs we can be more protected.
To update Windows, for example, we have to go to Start, go into Settings and go to Update and security. There they will show us the latest versions available and, if they are not installed, we can add them.
Beware of used programs
Another issue to keep in mind is the importance of using programs correctly. We must always install official software, which has not been modified by third parties and which will offer certain guarantees against others that we download from any site.
This is important to avoid computer attacks, since in many cases they use false programs to sneak Trojans and thus steal passwords or spy on us.
Common sense
We cannot leave common sense behind. It is essential to avoid making mistakes. For example, do not open attachments that come to us by email if we do not know the source that sent them or do not click on links that take us to sites that may be dangerous.
Normally, most computer attacks will require an error from the victim. Download something, click somewhere, etc. Therefore, if we avoid errors, we can significantly improve security.
In short, as we have seen there are different types of hackers but we can protect ourselves from all of them. It will be essential to be protected with a good antivirus, keep everything up to date and also avoid errors.