In the vast realm of cybersecurity, where complex algorithms and encryption technologies play a pivotal role, one of the most potent threats often comes not from lines of code, but from human psychology. Social engineering, a technique that exploits human behavior and trust, has become a prominent avenue for cybercriminals to breach digital fortresses.
Read on to learn about the world of social engineering, explore its various forms and tactics, and most importantly, learn some strategies to recognize and defend against these manipulative techniques.
Understanding Social Engineering
Social engineering is a psychological manipulation strategy that relies on human interaction and deception. It preys on individuals’ tendencies to trust, fear, or comply with requests from seemingly legitimate sources. Cybercriminals exploit emotions, curiosity, and the human desire to help, ultimately gaining unauthorized access to sensitive information or systems.
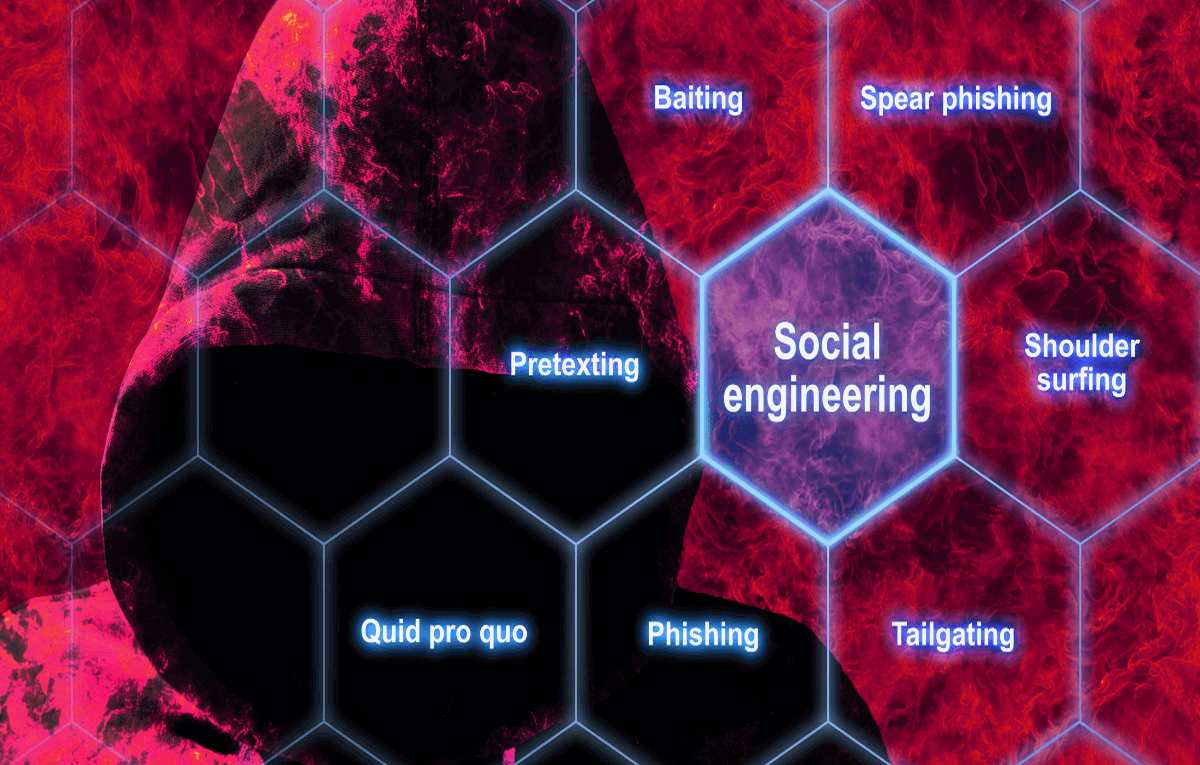
Common Forms of Social Engineering
Phishing: Cybercriminals send fraudulent emails or messages, often mimicking legitimate organizations, to trick recipients into revealing sensitive information or clicking on malicious links.
Pretexting: Attackers create fabricated scenarios or elaborate stories to manipulate individuals into divulging information or performing actions they normally wouldn’t.
Baiting: This tactic involves offering something enticing, such as a free software download or USB drive, that contains malicious software designed to compromise a system upon interaction.
Quid Pro Quo: Attackers promise a service or reward in exchange for information, often through unsolicited phone calls or emails. The information shared can then be used for malicious purposes.
Tailgating (Piggybacking): An attacker physically follows a legitimate employee into a secured area, exploiting their kindness or lack of suspicion to gain unauthorized access.
Recognizing Social Engineering
Thankfully, there are some common aspects of social engineering that you can be on the lookout for to better understand when you might be under attack. For example, attackers often create a sense of urgency or fear, pressuring and manipulating individuals to act quickly without thinking rationally. People often end up taking actions they wouldn’t normally consider as a result.
Those generating social engineering campaigns request sensitive information ASAP, too. While legitimate organizations rarely ask for sensitive information via email or phone, those involved in social engineering don’t work this way. As a result, you need to be cautious when sharing personal or financial details.
You can also pick up on social engineering by spotting unusual sender addresses on emails and other communications. Always check sender addresses carefully because cybercriminals often use email addresses similar to legitimate ones, with slight variations. Furthermore, if an offer or message seems too good to be true, it likely is. Cybercriminals use enticing offers to lure their victims.
Also, be wary of unsolicited communications that ask you to download attachments or click on links, especially if they’re urgent.
Defending Against Social Engineering
There are numerous steps you can take to defend against social engineering today. For example, take the time to train your staff. Regularly educate employees and individuals about the various forms of social engineering and how to identify potential threats. Encourage individuals to report any suspicious communication or activity to IT or security teams ASAP. Also, be sure to implement strict access controls in your business. Limit access to sensitive systems and information only to authorized personnel to minimize potential avenues for exploitation.
Another tip is to use strong authentication organization-wide. Implement multi-factor authentication (MFA) for email accounts and sensitive systems to add an extra layer of security. Plus, if someone requests sensitive information, verify their identity through an independent channel before sharing any details. In addition, when faced with unusual or urgent requests, take a step back and evaluate the situation before taking action.
Keep software, applications, and security tools up to date to mitigate vulnerabilities that attackers might exploit, and use anti-phishing software throughout your company. You can deploy anti-phishing tools that detect and block suspicious emails before they reach users’ inboxes.
Utilize network security management solutions, too. You can invest in robust network security management strategies to detect and prevent social engineering attacks at the network level. Utilize technologies such as intrusion detection systems (IDS) and intrusion prevention systems (IPS) to identify abnormal network behavior indicative of social engineering attempts.
Social engineering exploits human vulnerabilities, bypassing even the most advanced cybersecurity technologies. It’s vital to understand the various tactics used by cybercriminals and learn how to recognize and defend against them so that organizations can fortify their digital defenses.
Vigilance, skepticism, and ongoing education are essential to navigate the ever-evolving landscape of social engineering. By fostering a culture of cyber awareness and implementing robust defenses, we can collectively thwart these manipulative tactics and protect ourselves from falling victim to their insidious schemes.


