Hashing is the process of translating strings of characters into a code, making it much shorter and easier. Administrators encrypt files and messages to prevent unauthorized access to them. In this case the hash is used to help verify its integrity. Its function is to prevent the contents of a file from being corrupted or changed, and then present them as the original files.
The Pass the Hash attack can be considered as a lateral movement technique. This means that cybercriminals are using it to extract additional information and credentials after a device has been compromised. Thanks to this lateral movement between devices and accounts, these attackers can use the hash to obtain the correct credentials to eventually escalate our privileges. Thus, they can then access more influential systems, such as an administrator account on the domain controller. Most of this movement uses both a remote software program and malware.
It should also be noted that in Pass the Hash attacks, cybercriminals do not need to crack the hash. In this case they can reuse it or pass it to an authentication server. One thing you should know is that password hashes remain static from session to session until these keys are changed. For this reason, cybercriminals seek to obtain the authentication protocols of operating systems to steal our encrypted passwords.
Why does it affect Windows more?
If we have to enter our credentials every time we want to log in to a computer it can be an exhausting task. Especially if we have to log in to the system regularly. For this reason there are operating systems such as Windows that implement the single sign-on (SSO) For the users. This prevents them from having to re-enter their login credentials each time.
This way of working means that user credentials end up being cached within the system, making it easier for cybercriminals to access. One of those ways is through the use of the hash by the attackers with the Pass the Hash attack that I just mentioned in the previous section.
How does this attack work?
The moment we log into a Windows system for the first time, a hash of our password is generated and stored in system memory. At this time attackers have an opportunity for attackers to exploit your encrypted password.
The first thing a cybercriminal does is to obtain the hashes of the target system using any of the hash dump tools, such as Metasploit, Gsecdump, Mimikatz, fgdump, and pwdump7. This attacker will then use these tools to place the obtained hashes into a Local Security Authority Subsystem Service (LSASS). Thus, cybercriminals reuse our credentials to log in as if they were us, and then access all the applications and resources to which we have permission.
Pass the Hack attacks frequently target Windows computers, due to the security vulnerability of NTLM hashes, once administrator privileges have been obtained. Their aim is to trick a Windows authentication system into believing that they are the legitimate user, and then automatically provide the cybercriminal with the required credentials when attempting to access the target system.
If you want to carry out a successful attack, you have to access the LSASS and compromise a computer to such an extent that the malware can run with local administrator rights. By the time that Windows machine is compromised and the malware is deployed, it already has access to local usernames and NTLM hashes. The cybercriminal can then decide whether to look for more credentials, or try to access network resources using elevated user credentials.
How to protect yourself from this attack
The single sign-on protocol implemented with a hash is a useful feature to save users from having to re-enter their credentials. The problem is that cybercriminals take advantage of this feature single sign-on (SSO) to attack Windows computers and to a lesser extent also Linux and Unix systems. Now we are going to explain some measures to avoid being a victim of a Pass the Hash attack.
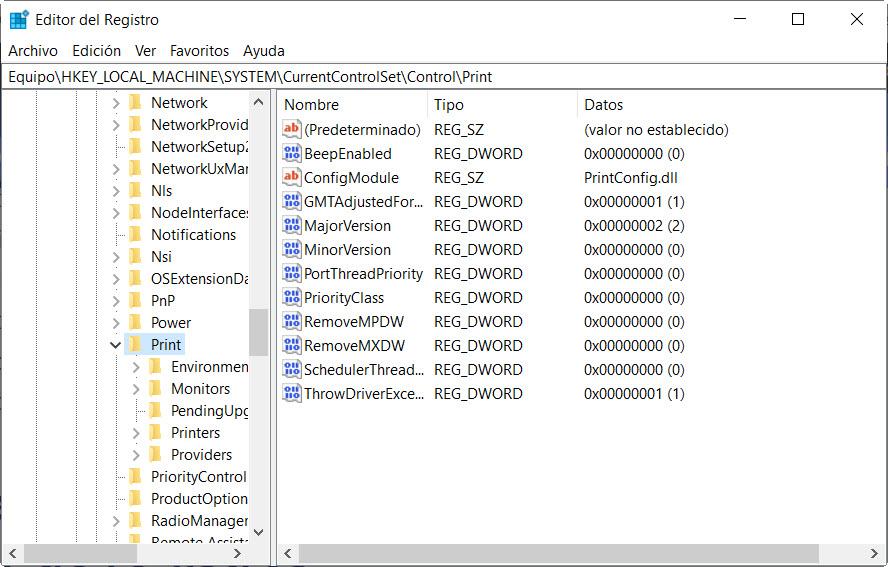
Turn on credential protection
In case you don’t know, Windows Defender Credential Guard is a security feature that Windows 10 and above systems have. Thanks to it we will be able to protect the confidential information stored in the system. The Local Security Authority Subsystem Service (LSASS) enforces the security policy on the Windows system.
We can activate this feature through the group policy, specifically we must go to the Group Policy Management Console, here we will have to go to the “Equipment configuration / Administrative Templates / System / DeviceGuard«. Once we are in this menu, we must click on «Turn on virtualization-based security» and enable the functionality. At the bottom we also have to configure the platform security level: secure boot, or use DMA protection and secure boot.
Once we have done this, we restart the computer and the changes will be applied.
Least Privilege and Two-Factor Authentication
In a least privilege model we have to limit access rights to users so that they can only use the resources and files necessary to do their job. We also need to remove unnecessary administrator rights and grant privileges only to trusted applications. In addition, it is convenient to review all the accounts and eliminate those that are not used, especially the administrator ones. This will reduce the attack vectors that a cybercriminal can use.
On the other hand, a two-factor authentication using tokens should also be applied.
Restart computers after logout
The reason for performing this task is that the system stores the password hash in its memory. If we restart our computer after closing the session, that hash will be deleted from the system memory. For this reason, instead of logging out and leaving the computer on, it is highly recommended to restart it or shut it down altogether to clear the hash from memory and greatly mitigate this new attack.
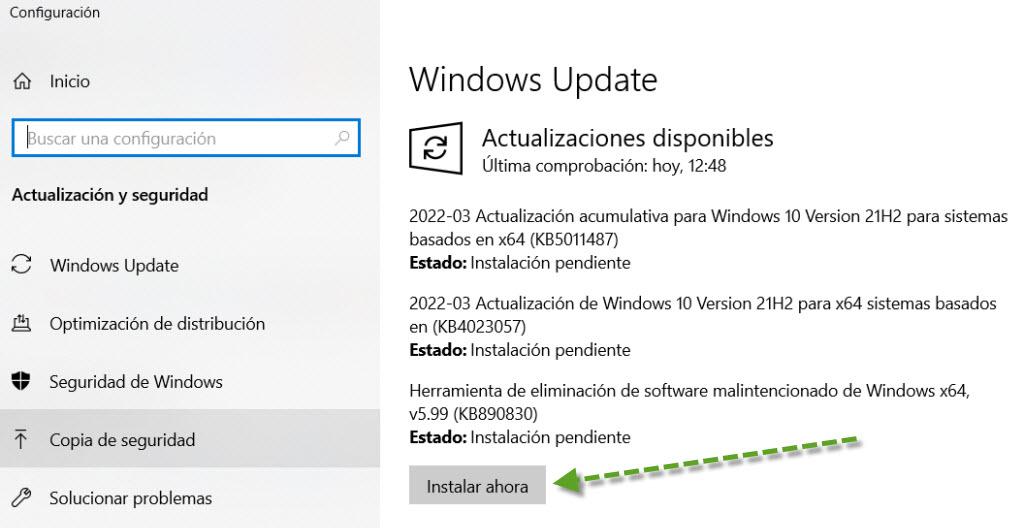
Update the operating system
Updating our operating system is a good idea as it fixes security flaws that could be exploited by cybercriminals.
On the other hand, it is advisable to use automated tools, such as anti-malware software. The reason is because they are useful for defending against a Pass the Hash attack and other types. These tools are capable of detecting infected or harmful files within our computer and then neutralize them before they attack. Finally, we could also completely encrypt the hard drive to prevent them from accessing the content of the drives and the NTLM hash that is stored on it, two options are to use Bitlocker, which is native to Windows, or use VeraCrypt, which is a solution completely free.
As you have seen, we have several options to protect ourselves from a Pass the Hash attack and to be able to mitigate this attack.