Main features
Rustcat is a program that allows us to open a socket on our computer, in order to accept incoming connections and to be able to check if there is communication with another computer that acts as a client. This can be done for several purposes, for example, to check if everything is correct at the network level, if the configured routing table is correct, and even if we have a firewall allowing or denying the different TCP and UDP connections to our device. Having a tool like Netcat or Rustcat when we are going to configure a server is essential, thanks to this tool, we can check if there is point-to-point connectivity, just by opening a certain port on the firewall.
If we did not have tools such as Netcat or Rustcat, we would have to listen to a web or FTP server on different ports to check if they are open correctly and listening, however, with these servers we would have to modify the configuration file, try with a web client or FTP client and later verify if the connection is successful or not. Programs like Rustcat greatly facilitate this task of checking if a certain port is open or closed, just by executing a command on the server that is listening on a certain TCP or UDP protocol, and another command on the client or clients that are going to connect, to check if there is point-to-point communication.
This Rustcat tool has very interesting features, such as a complete history of executed commands, it is very easy to use, more than the popular Netcat that we all know, in addition, it also supports the UDP protocol (in addition to supporting TCP) and is capable of using colors in order to make it really visually intuitive to understand. This program is compatible with all Linux distributions, such as Debian, Ubuntu and Arch Linux among many others. However, if your operating system is not compatible, you will always be able to download the source code and compile it directly on your computer, in this way, it should work without any problem. Finally, this program allows you to build a reverse shell, in this way, we can remotely execute commands on the machine that is connecting to our server.
Installation and commissioning
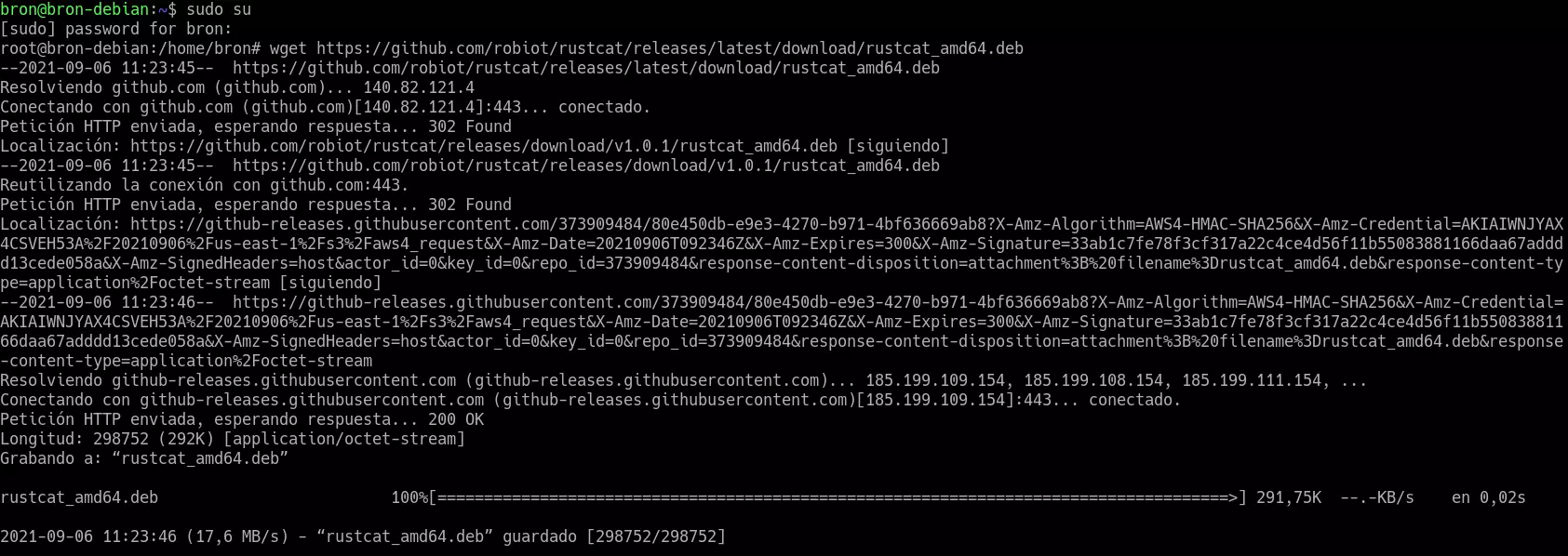
In our case, we have used an operating system based on Debian latest version to download and install this program, therefore, other distributions based on Debian such as Ubuntu or Kali Linux, among many others, will work perfectly and without problems. The first thing we have to do is download the .deb file in our operating system as follows:
wget https://github.com/robiot/rustcat/releases/latest/download/rustcat_amd64.deb
As you can see, this program has been downloaded directly from GitHub, to download the latest available version of the program which is v1.0.1 as you will see later.
Once downloaded, we will have to install it by executing the following command:
sudo apt install ./rustcat_amd64.deb
We could also install it using the popular dpkg command, but we think that doing an “apt install” is easier because it is widely used by all system administrators to install programs from repositories.
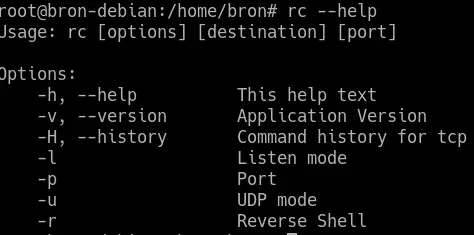
Once it is installed, we can start working with it, executing the “rc” command followed by the different commands, to check that it works correctly, you can run the program’s help with the following command:
rc --help
Once we have executed it, we will see all the available orders:
Once we have verified that the installation has been successful, we will see all the configuration options that we have available.
How Rustcat works
The operation of Ruscat is very simple, it is only necessary to execute the command «rc» followed by the different options and parameters, specifically, the syntax that we must follow is the following: rc [opciones] [destino] [puerto]. As for the available options, we have the following:
- -h or –help will show help with the list of available options
- -vo –version will show the version of the program, in our case, the latest version is Rustcat v1.0.1.
- -H or -history will show all TCP history
- -l will enable listening mode for the server
- -p allows you to select the port
- -u allows to configure UDP mode instead of TCP protocol
- -r enable reverse shell mode
Once we have seen the syntax and all the available options, we are going to give you some basic examples and other more advanced ones.
If we want to run Rustcat on our computer (localhost) and on port 33333 with TDP, we can do it as follows:
rc -l -p 33333
It could also be put in the following way:
rc -lp 33333
If we want to run Rustcat on our computer (localhost) and on port 33333 with UDP, we can do it as follows:
rc -l -p -u 33333
It could also be put in the following way:
rc -lpu 33333
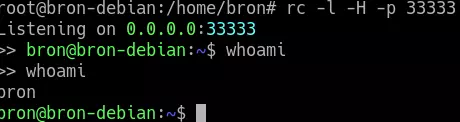
If we want to run Rustcat on our computer (localhost) and on port 33333 with TDP, but we have a history of the executed commands, we can do it as follows:
rc -l -H -p 33333
It could also be put in the following way:
rc -lHp 33333
If we want to listen on a specific IP address and not on all (0.0.0.0 means all interfaces), we must indicate it like this:
rc -l 192.168.1.2 33333
As you can see, thanks to the reverse shell we can execute different commands in bash easily and quickly. Rustcat is a very interesting alternative to the popular Netcat, although it is not installed by default. Thanks to this interesting tool, we will be able to check if our firewall is filtering communications from inside the local network or from outside, in order to test different ports and see if both TCP and UDP are open or closed.
We recommend you visit the Rustcat project on GitHub where you will find the source code and all the details about this great free tool for our Linux servers.