The first thing we are going to do is know what a hash is and what it can be useful for. Then we will see with HashCheck what are its main features and the minimum requirements to use it. Next, we will see how it is installed and some examples of use.
What is a hash and when can it be useful to us?
A hash we could define it as a unique fingerprint of the digital data of a file. Thus, for example, if the data in the file changes, after this modification, we will see how that hash changes completely. Basically we are going to use a hash in these two situations:
- To check whether a file has been modified or not.
- After downloading a file from the Internet, to verify that it is not corrupt, or that it has been modified with malicious intent by a cybercriminal.
The moment we modify a file, the alphanumeric code that we have as output in the hash, changes completely. Another thing you should know is that, by having the hash of a certain file, it does not allow us to recover the original file. On the other hand, among the currently most used hashes, we have the MD5, SHA1, SHA2-256, SHA2-512 and the last available has been the SHA3.
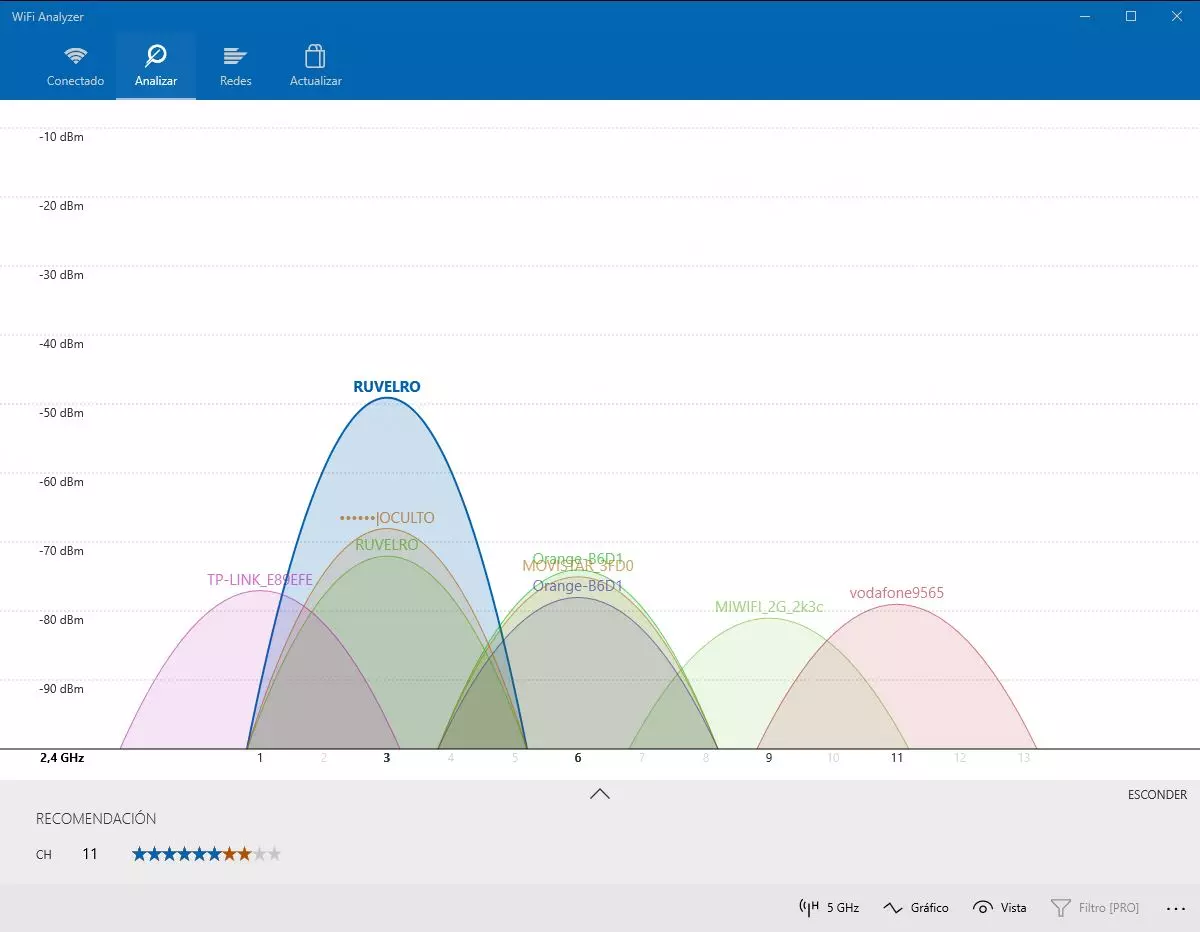
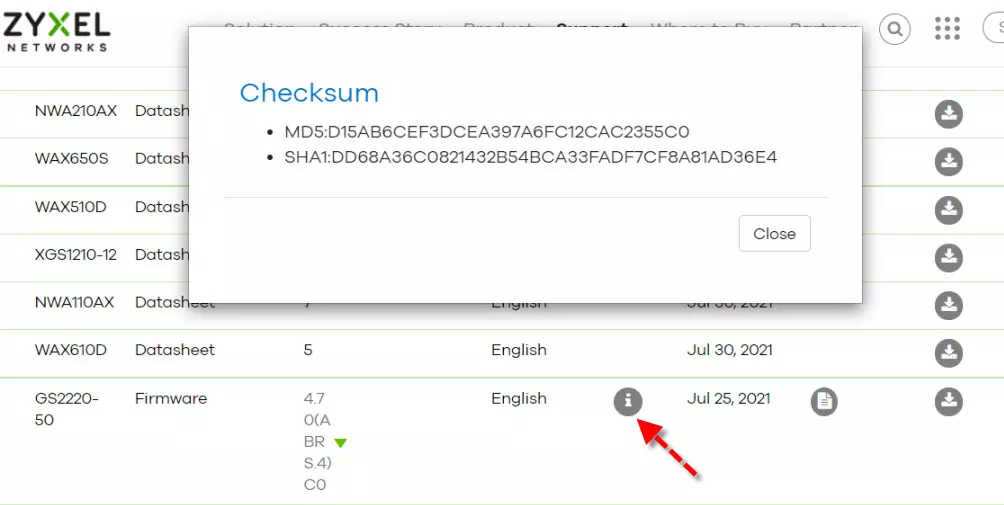
Imagine for a moment that you have to download the firmware of a router, an access point or a program for our PC. In the event that, after the download, that firmware was corrupted, and then we began the update, we could render that electronic device useless. For this reason, some manufacturers’ websites make it easy to hash their files to verify that the downloaded file is identical to the original.
In this example, with a software that could generate a hash that supports the MD5 or SHA-1 algorithm, we could check it with the Checksum that this manufacturer is offering us. Thus, in the event that the hashes were the same, we can proceed with the installation of that firmware with complete peace of mind. On the other hand, if it is not the same, we will know that it is wrong and we will not have to carry out that update. A program that we can use to carry out this task is with HashCheck, which we will talk about next.
HashCheck: features and operation
HashCheck we can define it as a program gratuitous to Windows which allows us to calculate and verify hashes. In addition, it also integrates into the Windows file explorer through a context menu and allows us to generate an MD5 file with the hash of all the files found in that folder. On the other hand, it also allows that, when we run the program again, make a comparison of the file values with the new hashes and thus know if the files are identical, or on the contrary they have been modified.
With HashCheck we are going to get all these features and functions:
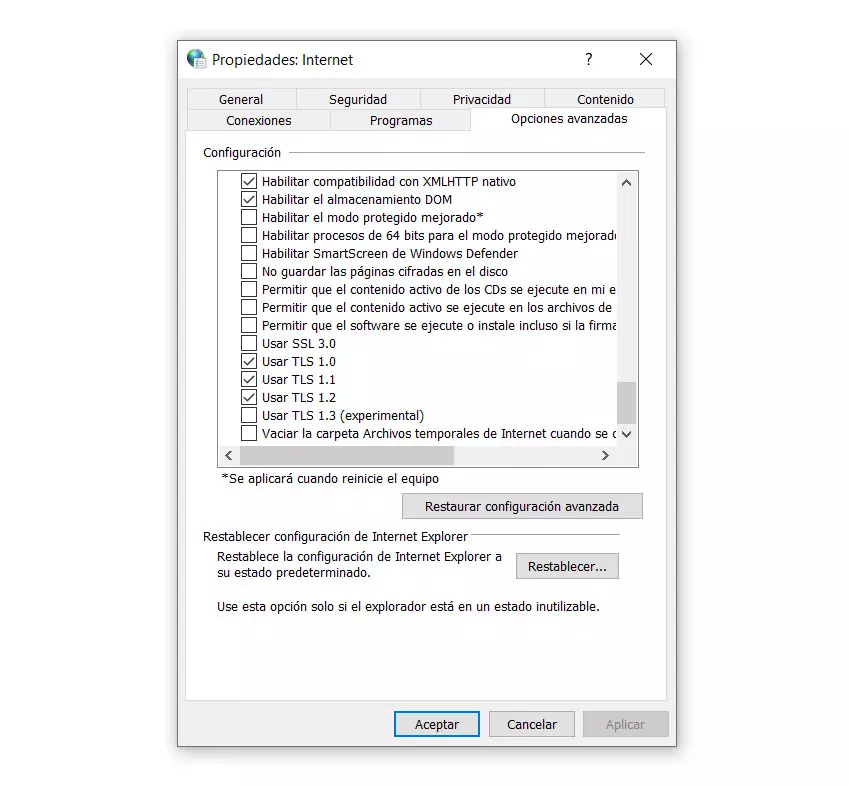
- Allows verification and verification of a hash, using files with a file extension of .sfv, .md4, .md5, or .sha1.
- Integration in the file properties of a new tab called «Checksum» where we can see the hashes of the files.
- It is a free and open source program. This implies that it can be used by everyone and that people with some knowledge of the C programming language can customize it to their liking.
As for the minimum requirements of the program, we must have a computer with at least Windows XP. It should also be noted that it is compatible with both 32-bit and 64-bit versions. As for the hard disk space, it will be less than 1 MB and, in addition, it should be noted that it has been translated into many languages, including Spanish.
Installation and first steps with HashCheck
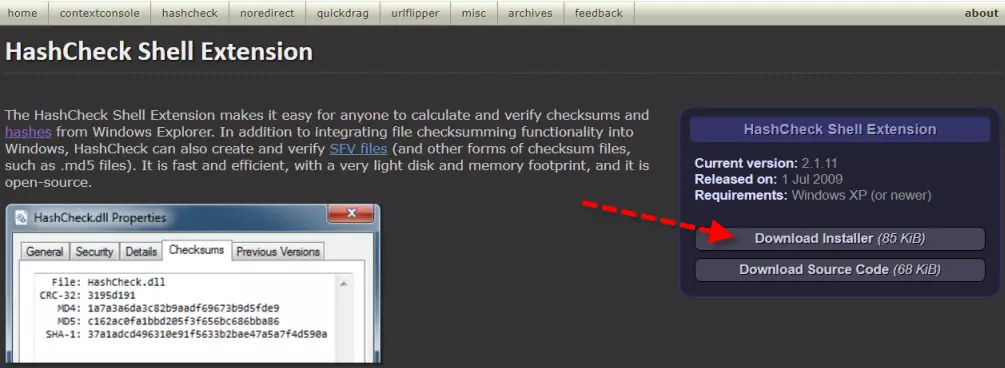
The first thing we have to do is download it from its website, for which we will click on this link. Then we will see a screen like this:
Next, click on the button Download Installer and we downloaded the installer. Once downloaded we execute it and we will get a screen like this:
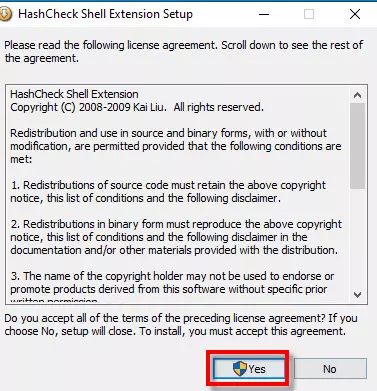
Then we click on And it is to accept the license agreement. Once the installation is finished successfully we will see this and click on accept.
I have performed the installation on a Windows 10 64-bit computer and the program has worked correctly.
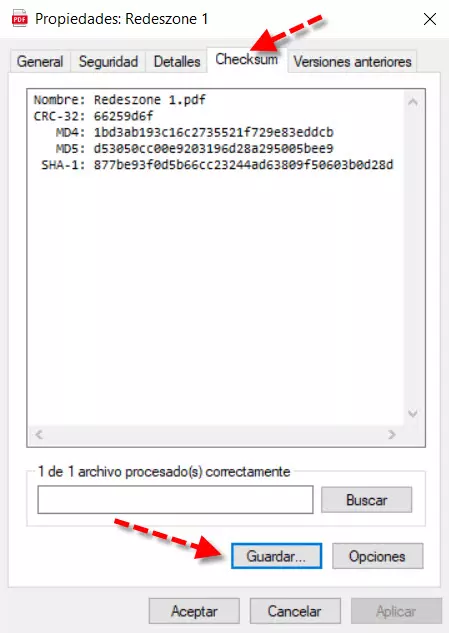
Now we are going to start working with a file. If you click on a file with the right button of the mouse from Windows Explorer and click on «Properties»You will see that a new tab has been added that previously did not appear called CheckSum.
Here we will be able to see both the file name and the hash algorithm in CRC-32, MD4, MD5 and SHA-1 formats. If we click on Keep, we will be able to store it on our hard drive with the hash algorithm that we want. In this case, the default is MD5, but you can select the one that interests you the most.
With HashCheck the way of working is different, we do not have a shortcut to access it from the Windows Menu nor can we create a shortcut to the program’s executable.
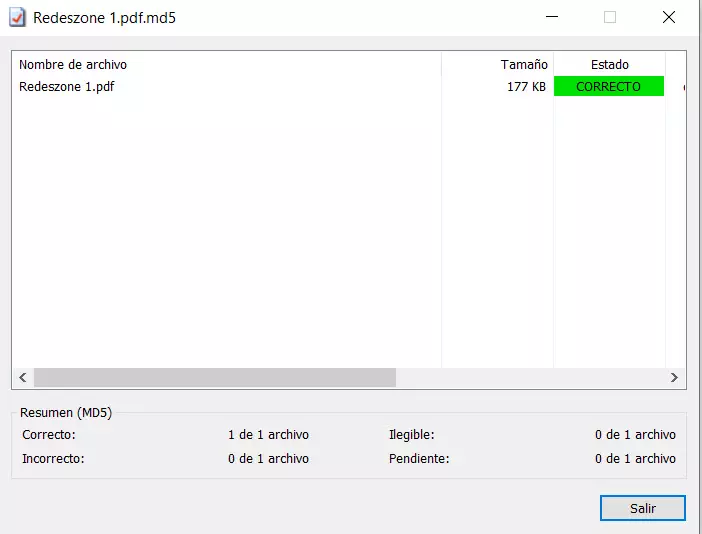
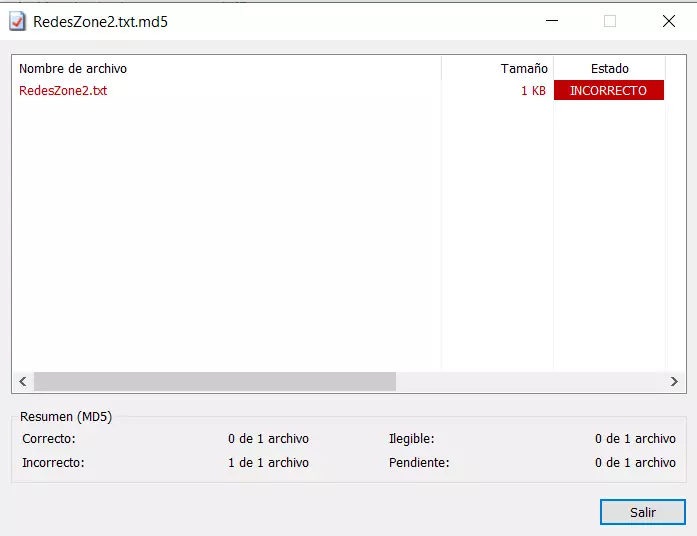
The only thing we have to do to access the program is to double click on the hash file that you have saved before. Then we will see a screen like this if the file has not been modified.
On the other hand, if we create a text file, save its hash and later modify it, it will detect that changes have occurred.
Working with folders
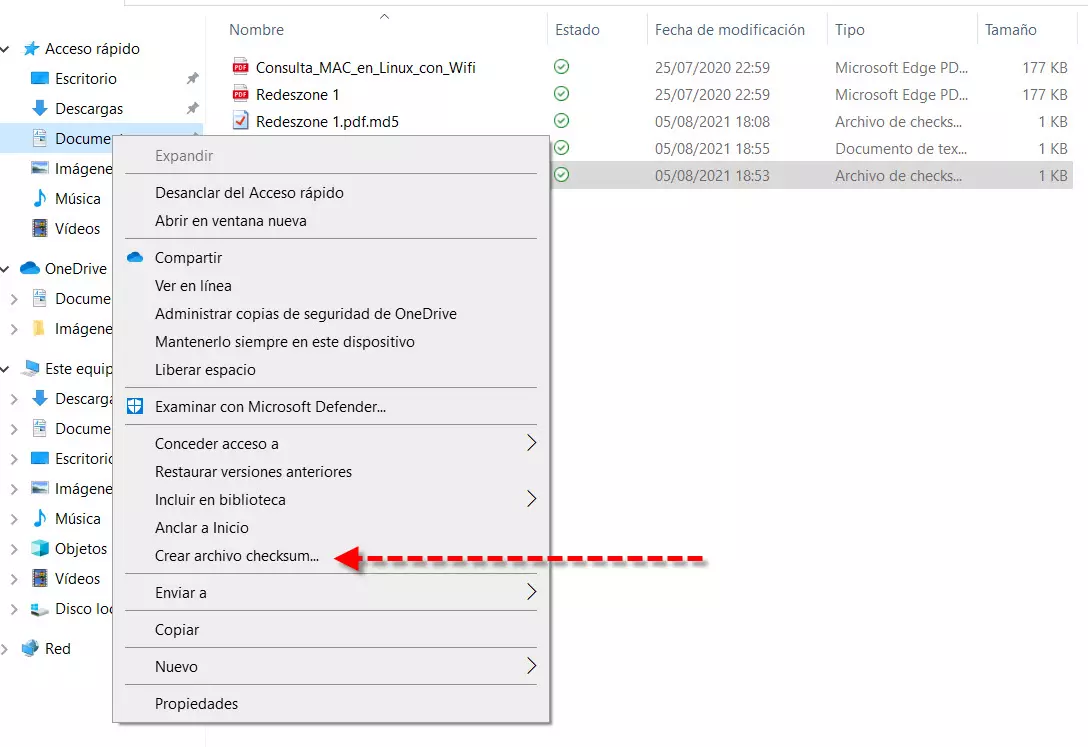
We have already seen how to work with a single file, but we also have the possibility of working with folders that contain several files. In this case things change and the way to do it is different. What we have to do is press the right mouse button and select the option create checksum file.
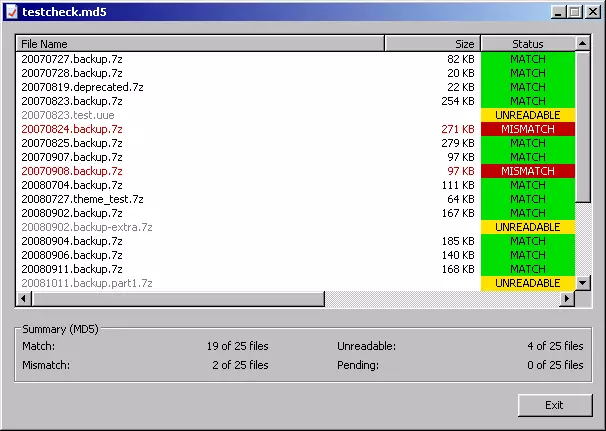
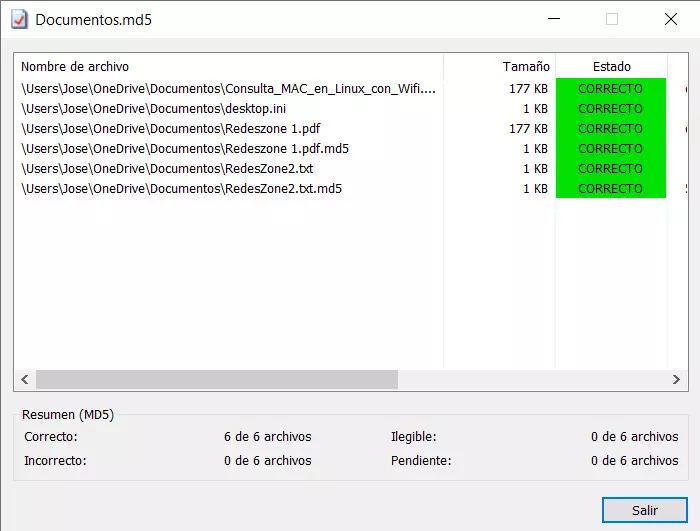
If we double click on that file that we have created we will be able to see if there has been any modification in the files in that folder.
In this specific case there have been no modifications. If it had been produced, some would be in red and it would be incorrect.
How to see the file hash without using this program
If we wanted to check the hash of a file and folder but did not have HashCheck installed, we could do it as follows:
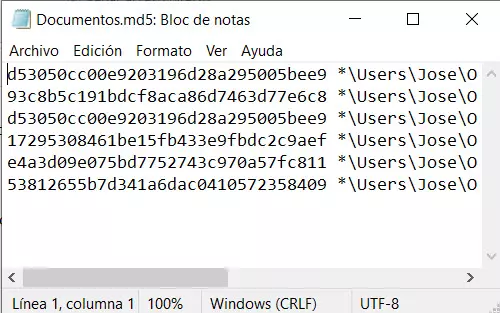
- We get on top of the hash file that we have created.
- The right button of the mouse, To open with and we choose memo pad.
Then we would see the hash algorithms stored in that file:
As you have seen, thanks to HashCheck we will be able to calculate the hash of any file and also of all the files contained within a folder. A positive point is that it is completely free, open source and very easy to use to check that your files have not been modified.