Currently there are very powerful and configurable programs that allow us to create a dictionary on demand, such as Crunch. If we know or intuit that the WPA password of a target has, for example, 10 characters and that it only uses uppercase and lowercase letters, we can create a dictionary that has all the combinations and permutations of uppercase and lowercase letters. This way, we won’t have to use dictionaries that are outside of these parameters. Crunch will allow us to configure the dictionary as we want, and it will export it to a text file for later use in programs like Aircrack-ng among others. We must bear in mind that this tool generates a dictionary with all the characters, generally a person puts an easy to remember WiFi password, and not a password that is almost random, so resorting to word dictionaries is a great decision.
Key Dictionary for WPA and WPA2
We currently have a large number of repositories on GitHub with text files with a large number of passwords that we can test. Of course, in the some dictionaries that we are going to put, we can find passwords that are not valid for WiFi networks because they are keys of less than 8 characters or more than 63 characters, however, we can use it without problems because the different programs to crack the WPA keys.
Probable-Wordlists
In the GitHub repository Probable-Wordlists, we will find a great list of password dictionaries that are specifically oriented to wireless WiFi networks. The author has taken dictionaries from other GitHub projects and has leaked all passwords that would not be valid for wireless WiFi networks. Therefore, we can be sure that all the keys that we test from this dictionary will work perfectly. We can download this dictionary of keys through GitHub itself or use the .torrent file to download it via P2P because it will surely work faster for you. The size of this dictionary is 8GB because it has millions of passwords filtered for years, but they are adapted to WiFi networks.
If we access the GitHub repository In full, we can find a large list of generalist key dictionaries, they are not specifically oriented to wireless WiFi networks, therefore, although we can use it, not all the keys that we test will be valid.
CrackStation
CrackStation is a free online platform that will allow us to crack password hashes based on some dictionaries that they have. In the event that we want to download the password dictionaries that they have on their platform, we can do so directly from here. The largest dictionary has a total of 1,493,677,782 words and occupies 15GB of space, we can download it from the web or use the BitTorrent network that will go much faster.
Another dictionary that we have available is a “small” version of the previous one, based on different leaks that have occurred over the years. In this list we have a total of 64 million passwords in the list and it occupies about 300MB uncompressed, therefore, we will also have a large number of words and keys to test when cracking a WPA key.
SecLists and Weakpass
At GitHub SecLists repository We will also find a large number of password dictionaries, however, in this case they are not adapted to WiFi wireless networks with WPA, therefore, you could try passwords that then really could never be. However, this repository is well known and widely used by security researchers.
In the WeakPass official website We can find a large number of key dictionaries that are designed for different uses, on this website we can find a large amount of information: size of the uncompressed dictionary, compressed size that we are going to download, the approximate time of cracking using different password hashes and also from WPA. For example, the largest dictionary will take us about 2 hours to test all passwords. All dictionaries can be downloaded through direct download or through the BitTorrent network. This website is highly recommended because it has many passwords for different leaks that have occurred over time.
Use these dictionaries with Aircrack-ng
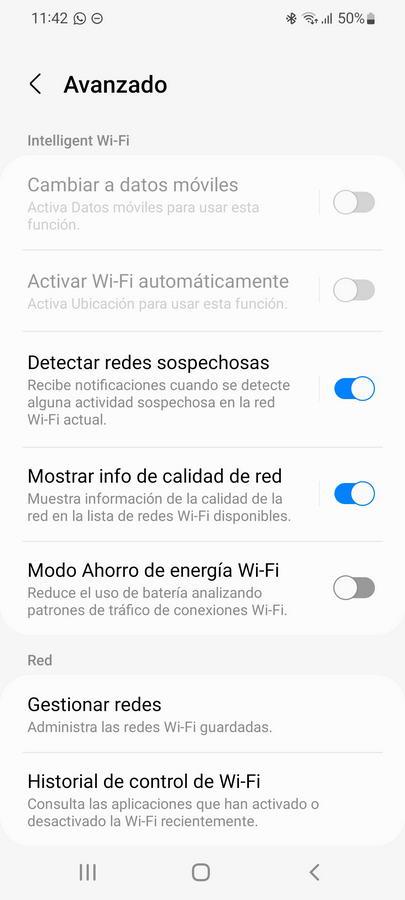
The Aircrack-ng program is the best known WiFi auditing tool that we can find today, along with hashcat to use the power of the GPU to carry out a brute force attack. In order to crack a WiFi network with WPA we need to do a total of three steps. The first step is to put our wiFi card in monitor mode and start capturing all the data to capture the handshake:
airodump-ng -c CANAL --bssid BSSID -w psk INTERFAZ
In case we have wireless clients connected to the AP or WiFi router, we could launch a deauthentication attack to speed up the handshake capture process, to do this we can execute the following command:
aireplay-ng -0 1 -a BSSID_AP -c MAC_CLIENTE INTERFAZ
Once the handshake is captured, and assuming that we have already downloaded the dictionary, we can use it with the following command:
aircrack-ng –b BSSID –w keys.txt captura-01.cap
The name of the airodump-ng capture is “capture-01”, the password dictionary is “keys.txt”, and the BSSID is the name of the WiFi network that we want to crack, since the Airodump capture captures all the handshakes that occur.
As you have seen, thanks to these password dictionaries for WPA and WPA2, we will be able to test all these passwords to see if we “got it right” with the password of the WiFi router or AP.