Mēris, remember that name. It is the biggest botnet in recent history. Using only a fraction of its punching power, it smashed the record for the biggest DDoS attack in history.
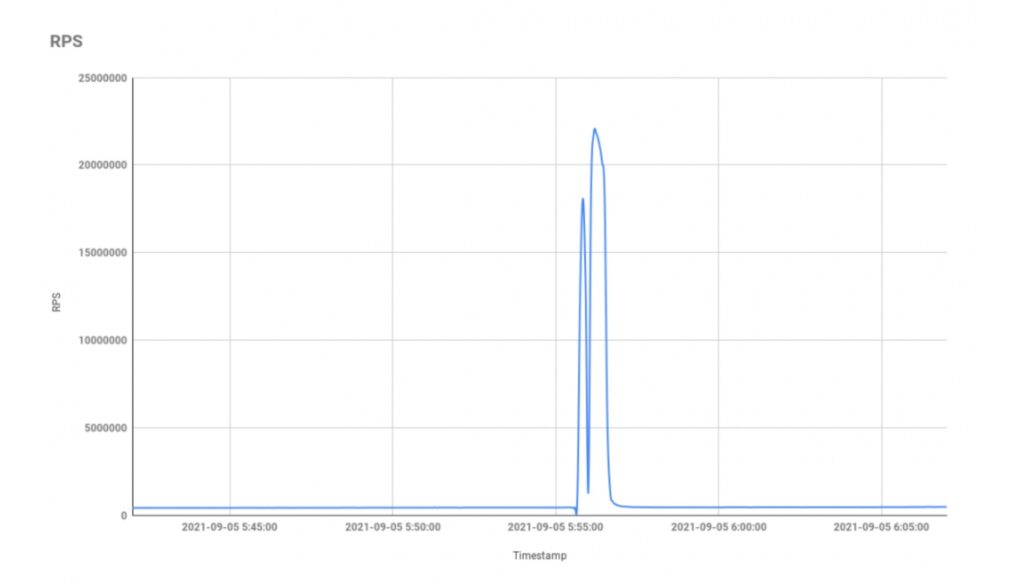
21.8 million requests per second, enough to overload and bring down gigantic computer networks. During September, the Russian search engine Yandex continued to experience waves of malicious connections, until the peak of connections, on an unprecedented scale. In the jargon, we speak of a denial of service attack (or DDoS) to designate this type of malicious act. Cybercriminals launch them through botnets, sets of corrupted machines that obey their command center, and allow them to create mass effects.
After the unprecedented spike, Qrator Labs, the Russian company in charge of protecting Yandex from attacks, conducted its investigation, the findings of which it published in a blog post. She traced it back to the botnet operator responsible for the attack, whom she decided to name Mēris (“the plague”, in Latvian).
The main objective of the gang is to extort money. He first threatens his victims by email: they can pay a ransom within a certain period or the group will unleash its botnet. Mēris is distinguished by a striking power much greater than those observed in recent years, which allows him to attack large groups, with large infrastructures.
The advantage for cybercriminals is that this kind of victim cannot economically afford to go offline. Results: They will be more inclined to pay the requested ransom in cryptocurrency.
A ” botnet of a new kind “
Qrator Labs describes its opponent as a ” botnet of a new kind “, And worries that he may” overload any infrastructure “. Usually, DDoS involves launching traffic to exceed the number of connections a server can collect. The flow (measured in gigabytes per second) becomes too important, and ends up cutting the Internet server.
The attacks launched by Mēris are of a different kind: the “RPS” (requests per second). They consist in sending requests whose goal is to overload the computing capacity of a server, and thus to overheat its memory and its CPU, two components at the heart of the functioning of computers. In other words, the requests will suck the computational capacity of the machine until it cannot take any more requests and breaks down.
The botnet only used an eighth of its strike force
The worst thing in history is that Mēris would only use a small fraction of his punching power. The peak demand was reached by the coordination of 30,000 machines. Problem: Qrator estimates that the botnet actually has more than 250,000 machines, more than 8 times more. It’s a truly impressive size: recent botnets rarely exceed 50,000 machines. In other words, Mēris is careful, probably so as not to attract too much attention from the authorities.
Researchers suspect all corrupted devices to be from the same small Latvian manufacturer, MikroTik. These would be relatively large machines, connected to high-performance internet connections, where most often the machines that make up the botnets are low-power connected devices, connected to a Wi-Fi network. The company has not yet reacted to this hypothesis.