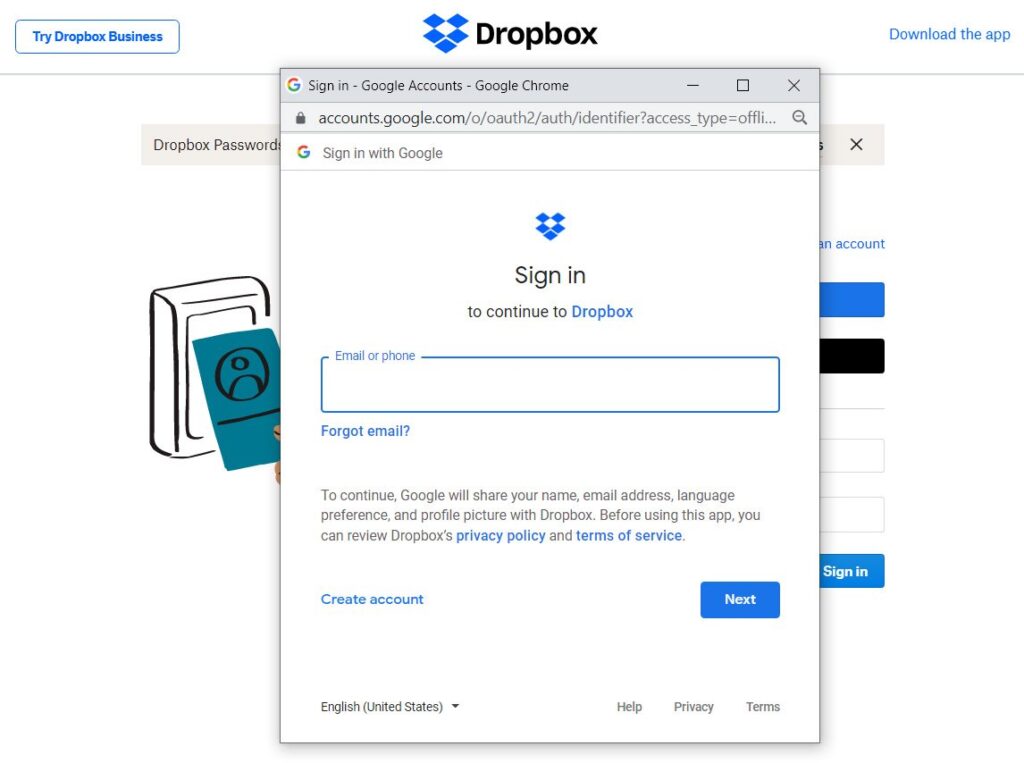
A new phishing toolkit recently created by a security researcher allows anyone to create login forms using fake Chrome browser windows. Normally, these windows appear when the service makes the login available from the credentials of other accounts.
To access a Dropbox account, for example, the platform allows accessing the service account with an Apple or Google account.
Clicking on any of them will open a browser’s Single Sign-On (SSO) window, asking the user to enter the credentials to access the Dropbox account.
The windows are stripped down and only show the fields for entering the credentials, and at the top, an address bar shows the URL of the login form.
Even though the address shown in the bar is disabled in these SSO windows, the user is still able to use the displayed URL to verify the legitimacy of the google.com domain. In this way, it is possible to verify the legitimacy before entering the login data.
While not a new trick, these pre-made windows in the new toolkit are different from those created in the past using HTML, CSS, and JavaScript. In general, these seemed out of the ordinary, which allowed for arousing suspicion.
Browser-in-the-Browser (BitB) Attack on Chrome
The new ‘Browser in the Browser (BitB)’ attack models were created by security researcher mr.d0x and made available by him on a GitHub account.
Basically, the attack creates fake popup windows inside legitimate browser windows (Browser in the Browser) to create convincing phishing attacks.
The templates created by mr.d0x hit Google’s Chrome browser for Windows and MacOS, with dark and light mode variants.
According to the researcher, the templates are very simple to use to create convincing windows in Chrome to display unique login forms on any online platform. “The redteamers (or group of pentesters) can simply download the templates, edit them to include the URL and title of the desired window, then use an iframe to display the login fields,” mr.d0x explained to BleepingComputer.
There is also the option to add HTML to the login form directly to the template, however, it would be necessary to align the form properly using CSS and HTML, warns the researcher.

Image: slyellow/Shutterstock
Models are available at researcher account on GitHub for those interested in testing.