Two new security flaws have just been discovered in Microsoft’s Teams application: one hides in the application’s tabs, the other targets invitations to join a discussion.

Teams is the Swiss army knife of messaging and videoconferencing applications. If the application was initially rather thin, it is clear that Teams continues to be enriched with new features. So much so, the software has succeeded in establishing itself as one of the most widely used messaging, video and document sharing applications in the world, especially in the professional world.
But the application is not free of bugs and especially security flaws. Two major issues have recently been discovered: the first relates to the tabs of the application, while the second is related to the links that you may have already received and which invite you to join a conversation.
Also read: Microsoft launches Teams Premium with features powered by ChatGPT
Malware can hide in Teams tabs
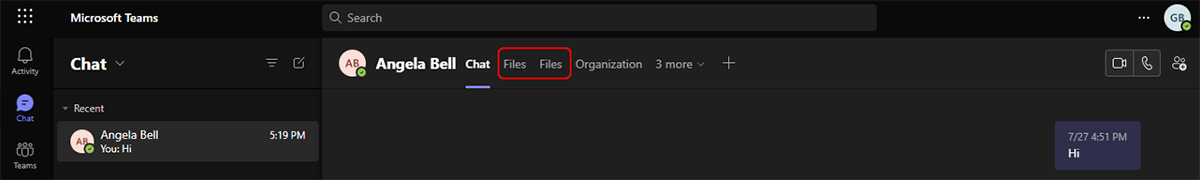
The first flaw spotted by Proofpoint concerns the tabs of Microsoft Teams, which allow third-party applications to dialogue with the application. Tabs are used in particular when you share a file on OneDrive, when you synchronize your calendar, etc.
The concern is that the use of these tabs can easily be diverted. According to cybersecurity experts at Proofpoint, an attacker can easily create a fake tab, like in the screenshot below, and hack any user. This false tab is then used to spread a phishing campaign, all that is more classic, but also lead to a web page on which malware is hidden, which then gives access to the Office 365 account of the victims.
A second flaw concerning Teams was also discovered by the same team specializing in cybersecurity. Rather than pointing to a web page, Tabs can redirect users to a file that automatically downloads.
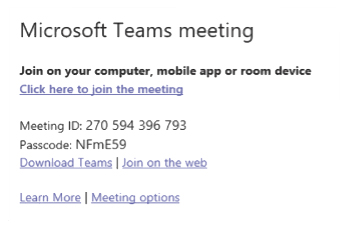
Beware of these fake invitations to join a Teams conversation
And that’s not all: an attacker can also alter a Teams invitation link. Here, the hack is even harder to crack, as the link looks legit. But in reality, it is the URL behind the link that has been changed. This same URL then redirects to a malicious site or executable.
Proofpoint believes that these threats are not to be taken lightly. Granted, the attacker must already have access to a compromised Teams account. But according to the company, 60% of Microsoft 365 users were victims of a “successful” takeover of their account in 2022. A figure that sends shivers down your spine.
Source : Proofpoint