Tempest attacks are a vulnerability of voting machines. This risk was recently pointed out by the director general of Anssi, Guillaume Poupard, in front of deputies.
Voting machines definitely do not win the votes. While these devices have been subject to a moratorium since 2008, the director general of the National Agency for the Security of Information Systems (Anssi) pointed out the risks associated with their use. This equipment is deployed in 66 French municipalities, bringing together nearly a million voters.
In a hearing at the National Assembly at the end of September, Guillaume Poupard shed light on the subject. Of course, voting devices make it possible to count the votes much faster, but do their advantages outweigh their disadvantages? ” One can imagine, for example, attacks which would seek to observe the behavior of a remote voting machine, and this is not science fiction, thus warned the senior official. If these voting machines are poorly designed, there is the danger that within ten or twenty meters, on the other side of the wall, it is possible for someone with bad intentions to pick up elements. It is not trivial, it requires a certain know-how, but it is not out of reach either.e. “

A type of attack long classified
So, what exactly is Guillaume Poupard talking about? Anssi engineers are in fact worried about the possibility of a Tempest-type attack. An English-speaking acronym, with the scent of the Cold War, whose real meaning we do not even know with certainty, according to Aurélien Francillon. ” It remained for a long time something very mysterious, because this technique, largely exploited by governments, remained classified », Explains this professor from the Eurecom engineering school, one of the subject specialists in France.
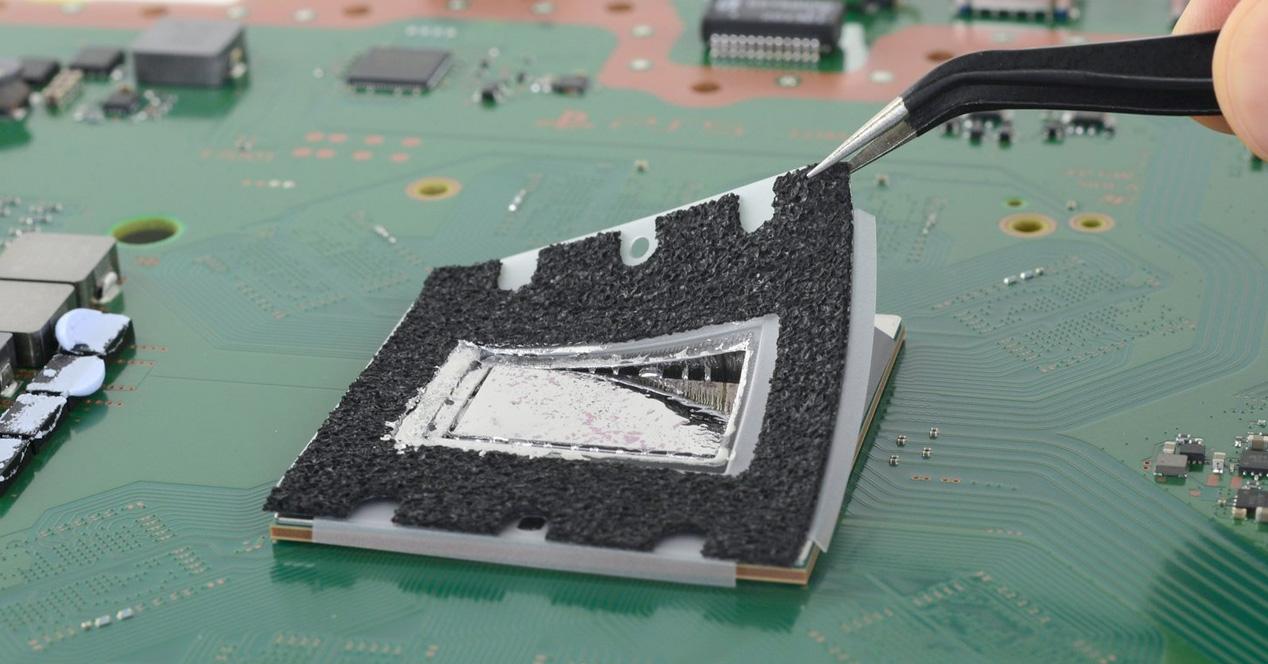
To simplify, this term refers to the interception and exploitation of electromagnetic disturbances of a material or a system, with a view to reconstituting the processed information. In other words, by listening to the electromagnetic activity of a device, an attacker will be able to spy on you. This can be the recording of a video signal, but also of the keyboard or the printer. If we already have a library of these signals, we can thus recreate, with these tapping, hidden data.
These mysterious Tempest attacks originated during World War II. ” Bell Telephone engineers are shocked to discover that they manage to intercept clear messages processed by the Signal Corps crypto center, using oscilloscopes from their lab across the street, 25 meters away ”, Explain in an article, Pierre-Michel Ricordel and Emmanuel Duponchelle, two agents of the laboratory Security of wireless technologies of Anssi.
A technique long reserved for spies
A domain reserved for spies, the Tempest attacks are still poorly understood today. But we have a few examples that show their potential. In 1945, the United States Ambassador to the Soviet Union was offered a seemingly innocuous wooden seal. It actually hides a passive listening device, activated by an electromagnetic signal. Much later, in 1985, researcher Wim Van Eck proved that it is possible to reconstruct what appears on a screen, by listening to a simple radio noise. Via the publication of a catalog of the American intelligence agency NSA, the German weekly Der Spiegel also revealed the keen interest that the spy masters have in these techniques.
Tempest attacks are no longer the preserve of secret agencies, however. Today, there is an open source tool that can reconstruct, in real time, the video image of a screen from parasitic signals, with the purchase of a radio receiver of around twenty euros.
We can therefore understand Anssi’s concerns about voting machines. If the latter were vulnerable to this attack, it would be possible ” to understand that such radio signal corresponds to such vote, and possibly, but this seems unrealistic to me, to know who used the machine during the vote, lists Aurélien Francillon. One can also imagine that the injection of faults would be possible. By sending a certain electromagnetic field, the attacker could alter the operation of the machine and make it make a mistake.. “
In a 2011 article, the former head of the operational cryptography and computer virology laboratory at Esiea, Éric Filiol, also stressed that voting machines are only guaranteed ” for an extremely limited local electrostatic field “. To disrupt a ballot, it would suffice ” to locally create a sufficiently large field by microwave devices, and to have the presence of this field established by a bailiff He pointed out. Such an operation would not be very discreet – it could jam the phone or the wifi, and would require large antennas. The question is whether we want to take this risk.